File Integrity Monitoring Analysis: Strengthening Cybersecurity with Proactive Measures
In today's digital landscape, cybersecurity threats are becoming increasingly sophisticated, putting critical systems and sensitive data at risk. One of the most effective ways to protect against these threats is through the implementation of File Integrity Monitoring (FIM) analysis.
What is File Integrity Monitoring Analysis?
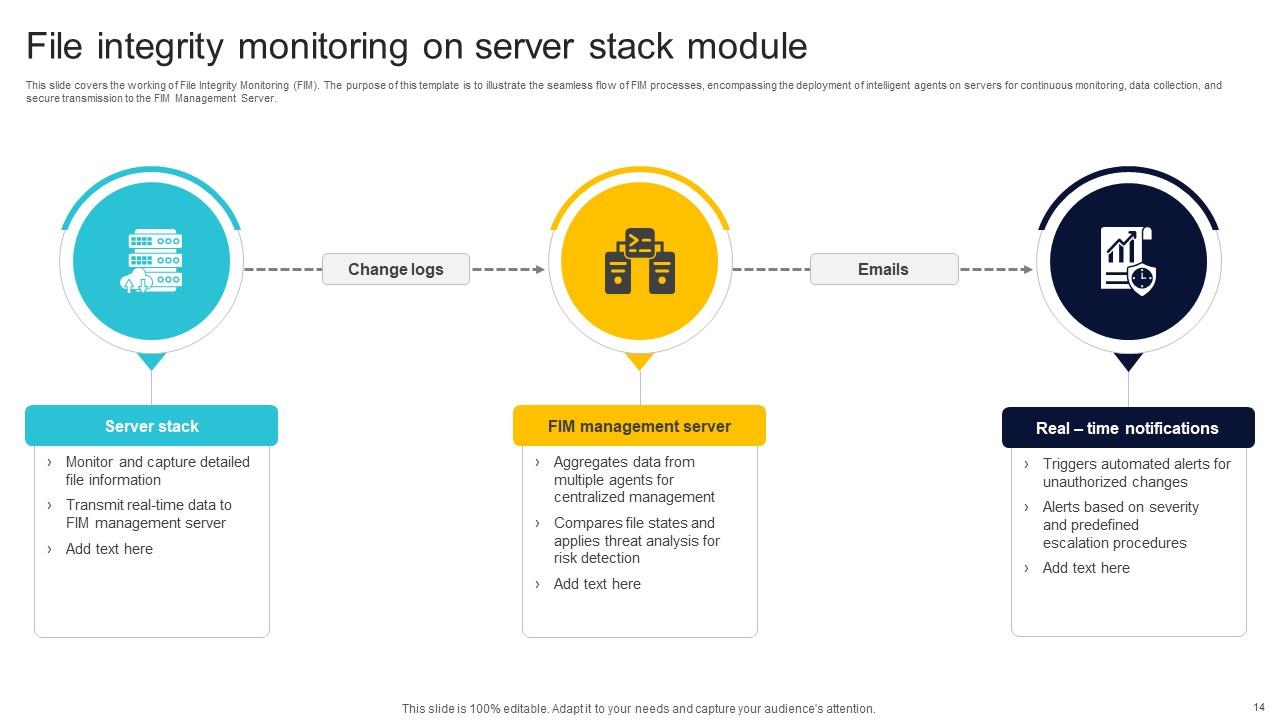
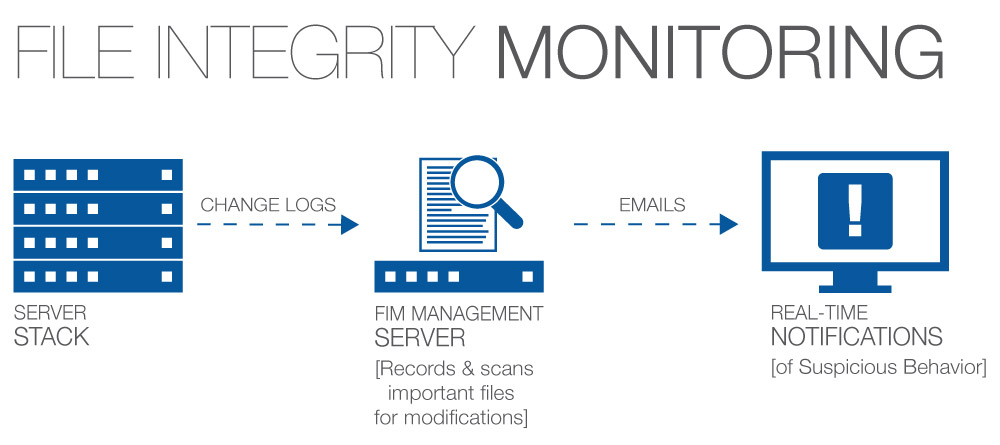
File Integrity Monitoring (FIM) analysis is a security process that monitors and analyzes the integrity of critical assets, such as files, system configurations, and databases, to detect signs of tampering or corruption. This proactive approach helps organizations detect and prevent unwanted modifications, ensuring the confidentiality, integrity, and availability of their systems and information.
Benefits of File Integrity Monitoring Analysis

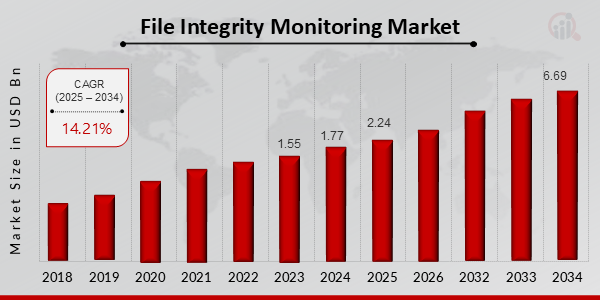
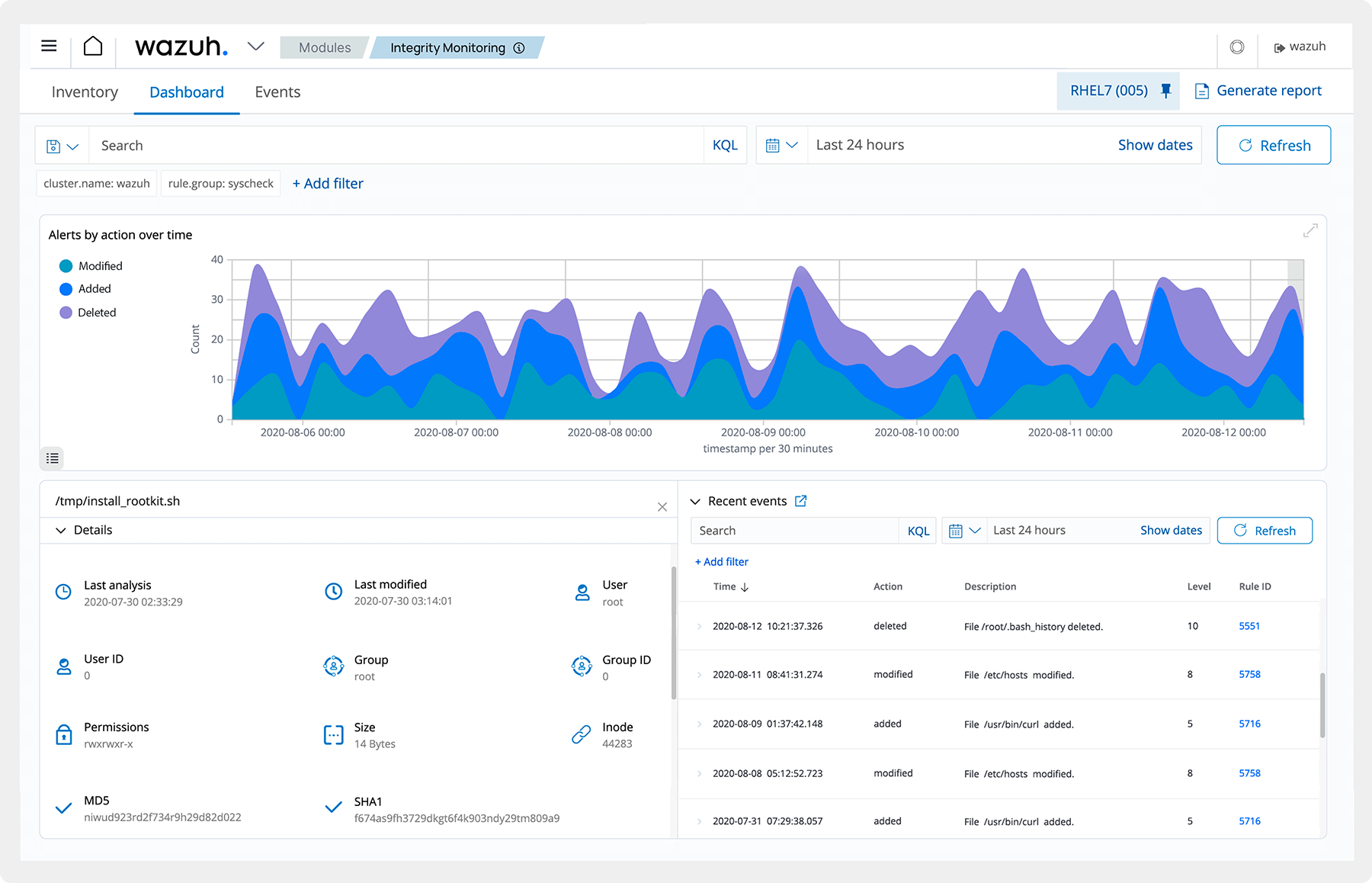
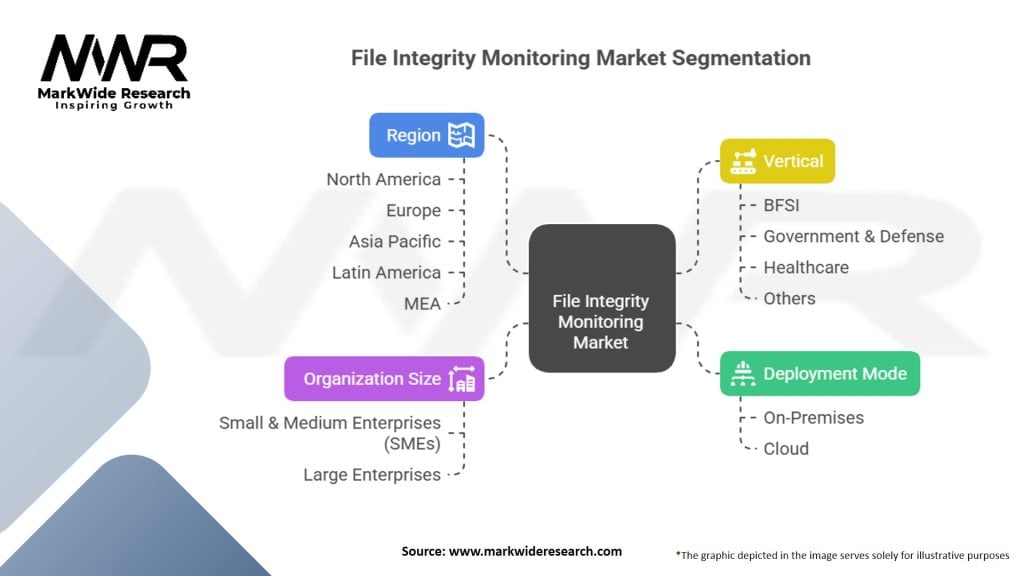
Furthermore, visual representations like the one above help us fully grasp the concept of File Integrity Monitoring Analysis.
- Meet compliance requirements: FIM analysis helps organizations meet regulatory compliance standards, such as PCI-DSS and ISO 17799.
- Real-time threat detection: FIM analysis provides real-time monitoring, enabling organizations to detect and respond to potential security breaches.
- Forensic analysis: FIM analysis provides a valuable retrospective analysis capability, allowing security teams to review historical data and understand the timeline of file changes, aiding in the forensic investigation of security incidents.
- Enhanced compliance and security: FIM analysis enhances compliance and security by monitoring and analyzing file changes, ensuring data safety, system functioning, and regulatory norms.
Implementing File Integrity Monitoring Analysis
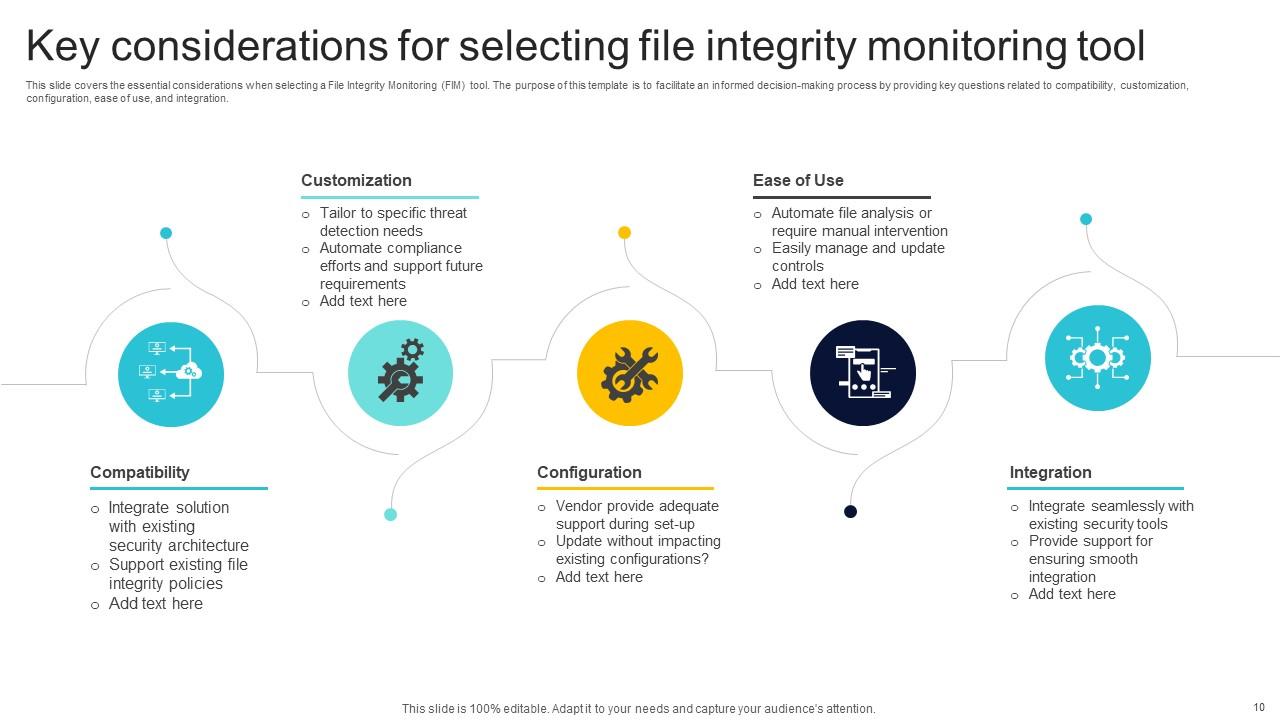
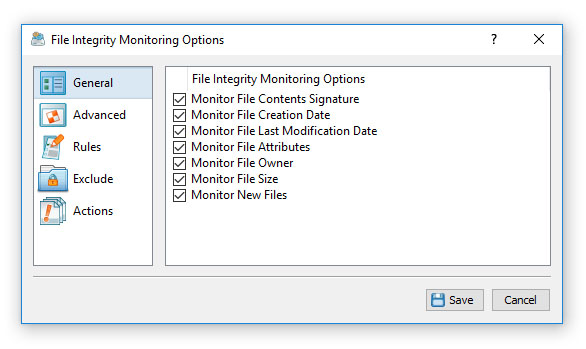
- Choosing the right tool: Selecting the right FIM tool is crucial, with options such as Wazuh SIEM, OSSEC, and Atomicorp FIM as a Service.
- Monitoring and analysis: FIM analysis requires continuous monitoring and analysis of file changes, system configurations, and databases.
- Compliance and security: FIM analysis must be integrated with compliance and security measures to ensure effective threat detection and response.
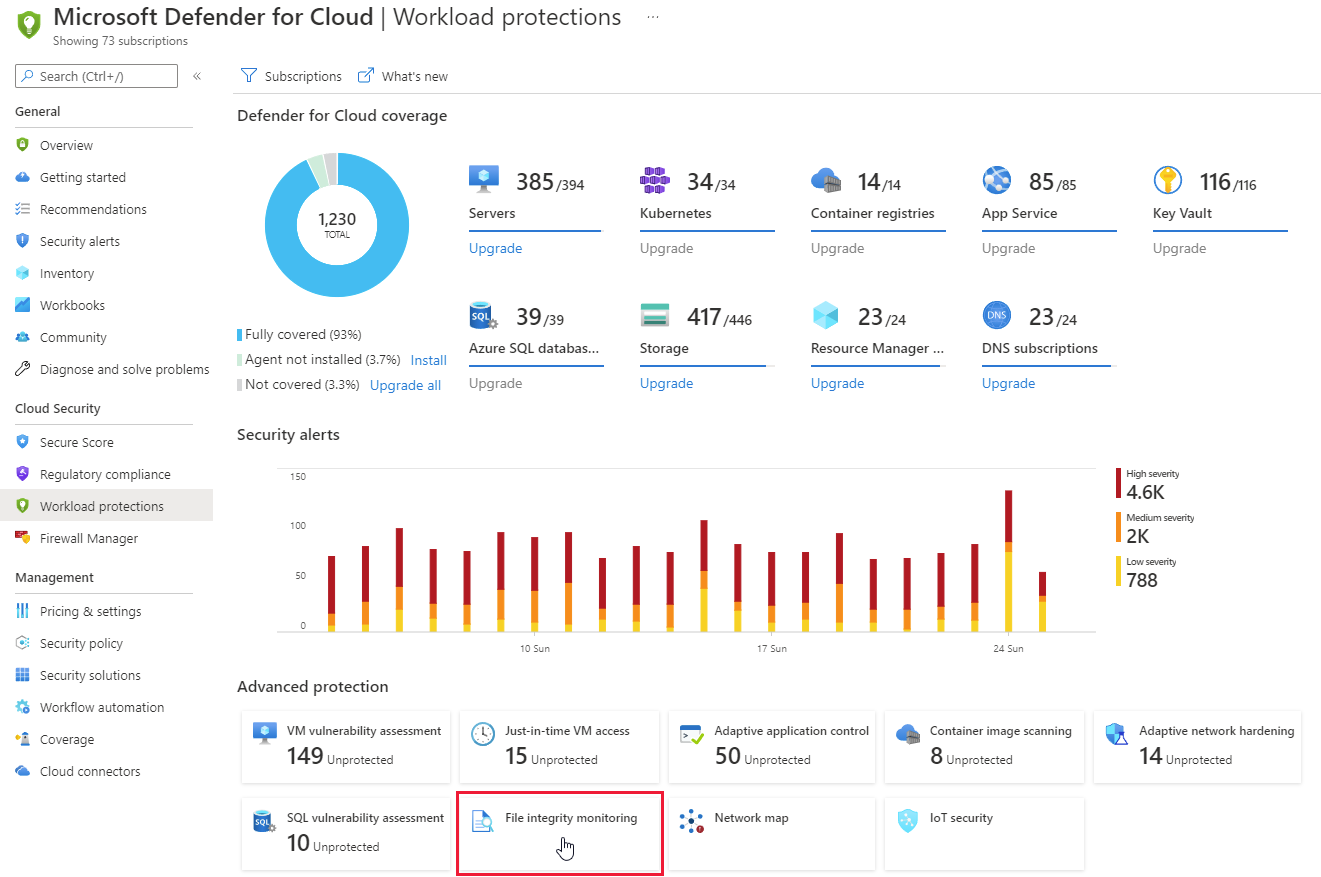
- Cloud security: FIM analysis must be adapted for cloud environments, ensuring effective real-time monitoring and incident response.
Top File Integrity Monitoring Solutions
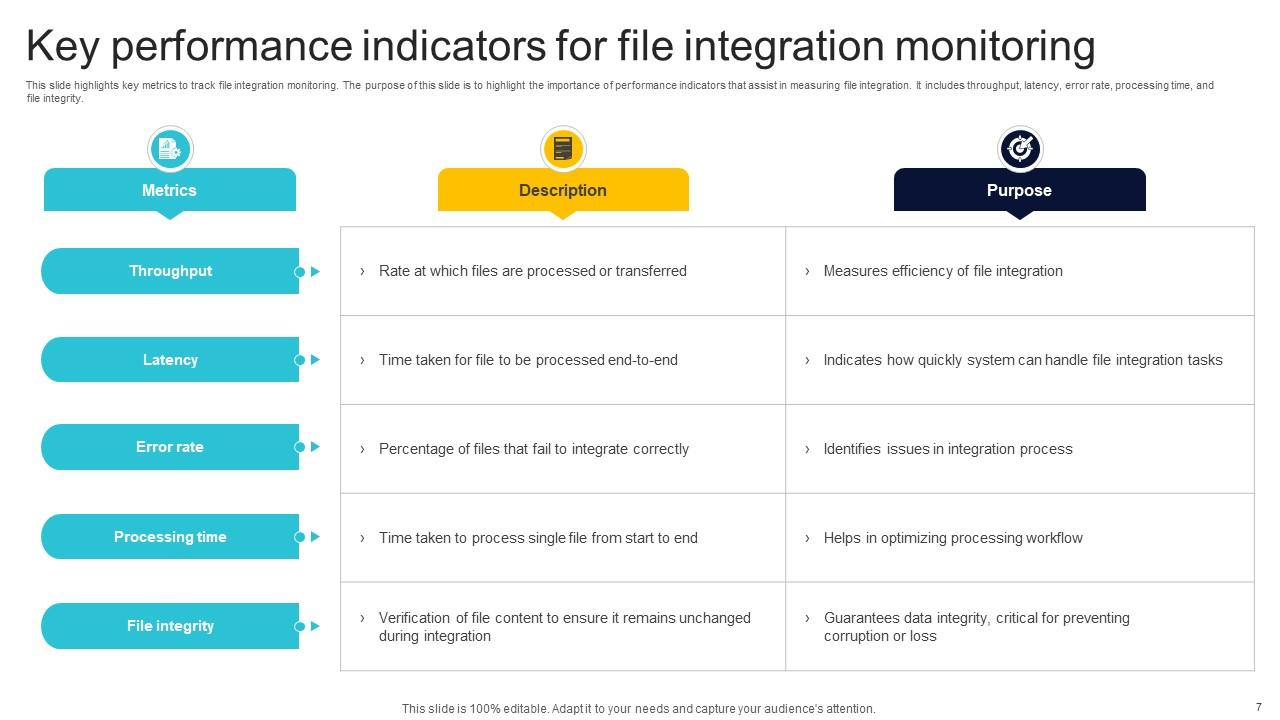
Moving forward, it's essential to keep these visual contexts in mind when discussing File Integrity Monitoring Analysis.
Several top FIM solutions are available, including:
Conclusion
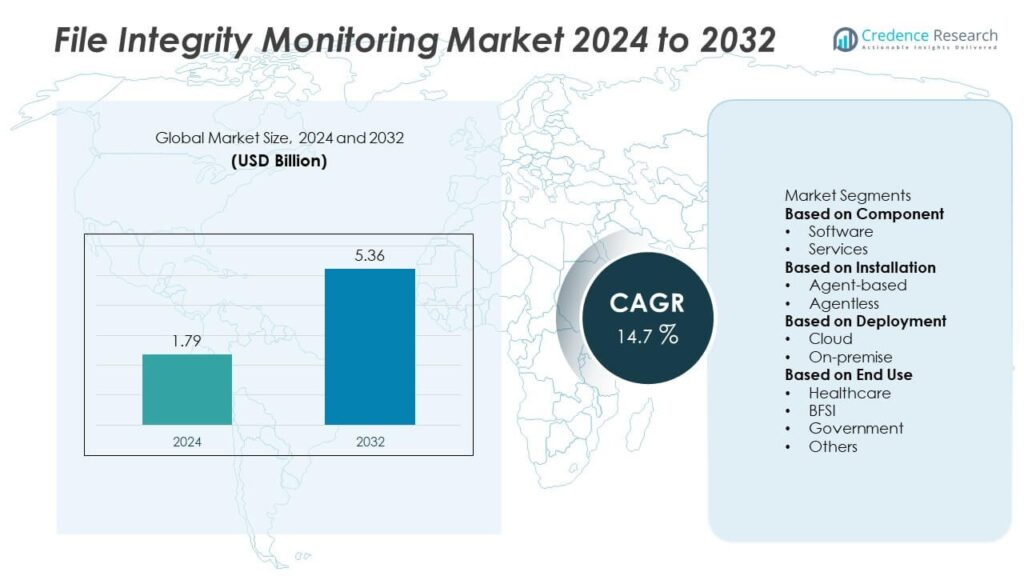
File Integrity Monitoring analysis is a critical component of proactive cybersecurity measures, enabling organizations to detect and prevent unwanted file modifications, ensure data safety, and maintain system functioning. By implementing FIM analysis, organizations can enhance compliance and security, real-time threat detection, and forensic analysis, ultimately strengthening their overall cybersecurity posture.
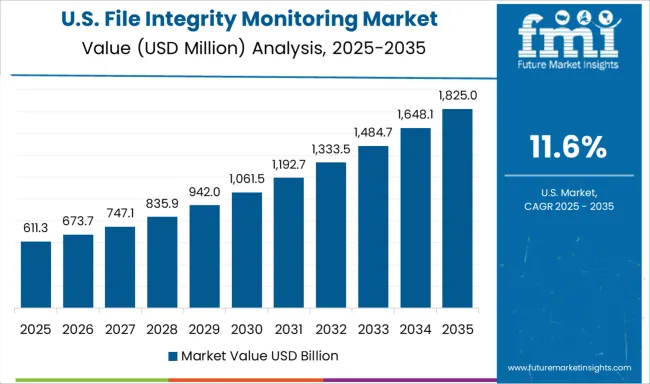
As the threat landscape continues to evolve, FIM analysis will play an increasingly important role in protecting critical systems and sensitive data. By understanding the benefits, implementing the right tool, and staying up-to-date with the latest best practices, organizations can ensure they are well-equipped to face the growing threat of cybersecurity attacks.





![[시장보고서]파일 무결성 모니터링 시장 분석 및 예측 (-2035년) : 유형별, 제품 유형별, 서비스별, 기술별, 컴포넌트별 ... View of [시장보고서]파일 무결성 모니터링 시장 분석 및 예측 (-2035년) : 유형별, 제품 유형별, 서비스별, 기술별, 컴포넌트별 ...](https://orthoplexsolutions.com/wp-content/uploads/2025/01/file_integrity_monitoring_2nd_section-scaled.webp)