Best Practices for Data Protection: Shielding Your Organization from Cyber Threats
In today's interconnected digital landscape, protecting sensitive data has become an indispensable aspect of any organization's security arsenal. As data breaches and evolving regulations continue to make headlines, understanding the best practices for data protection has become crucial for businesses and individuals alike. In this article, we will explore the key components and best practices for building a robust data protection framework.The Building Blocks of a Strong Data Protection Framework
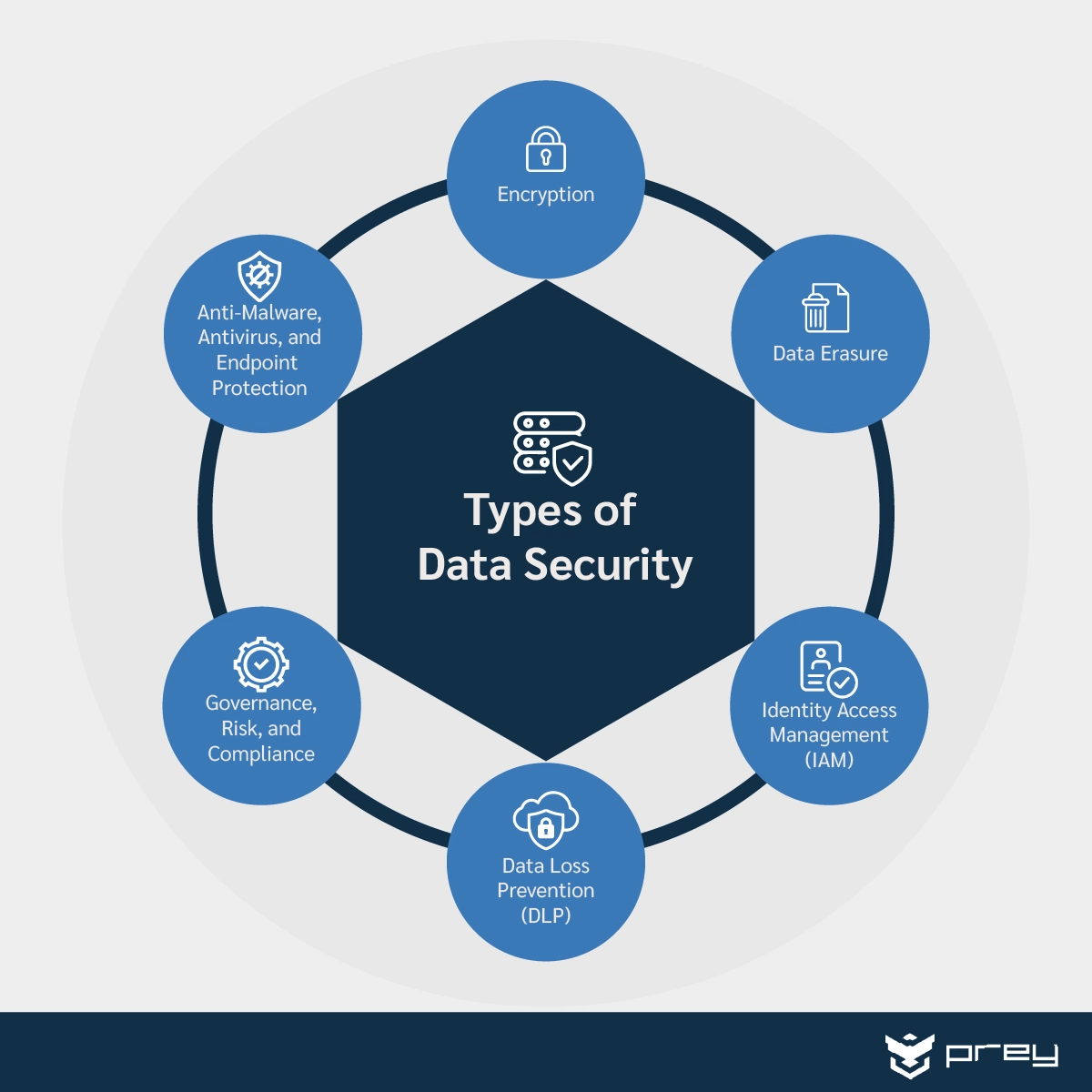
While every data protection strategy is unique, several key components and best practices underpin a robust framework. These include: *Encryption
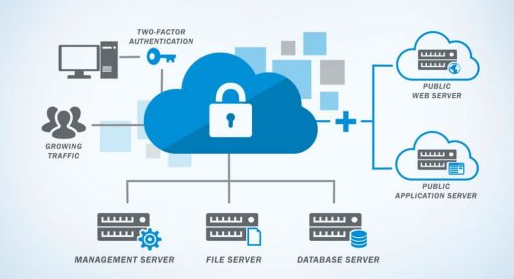
- Encrypting sensitive data both in transit and at rest provides an additional layer of security, making it challenging for unauthorized parties to access it. *Access Controls and Authentication
- Implementing strong access controls, such as multi-factor authentication, ensures that only authorized individuals can access sensitive data. *Regular Backups

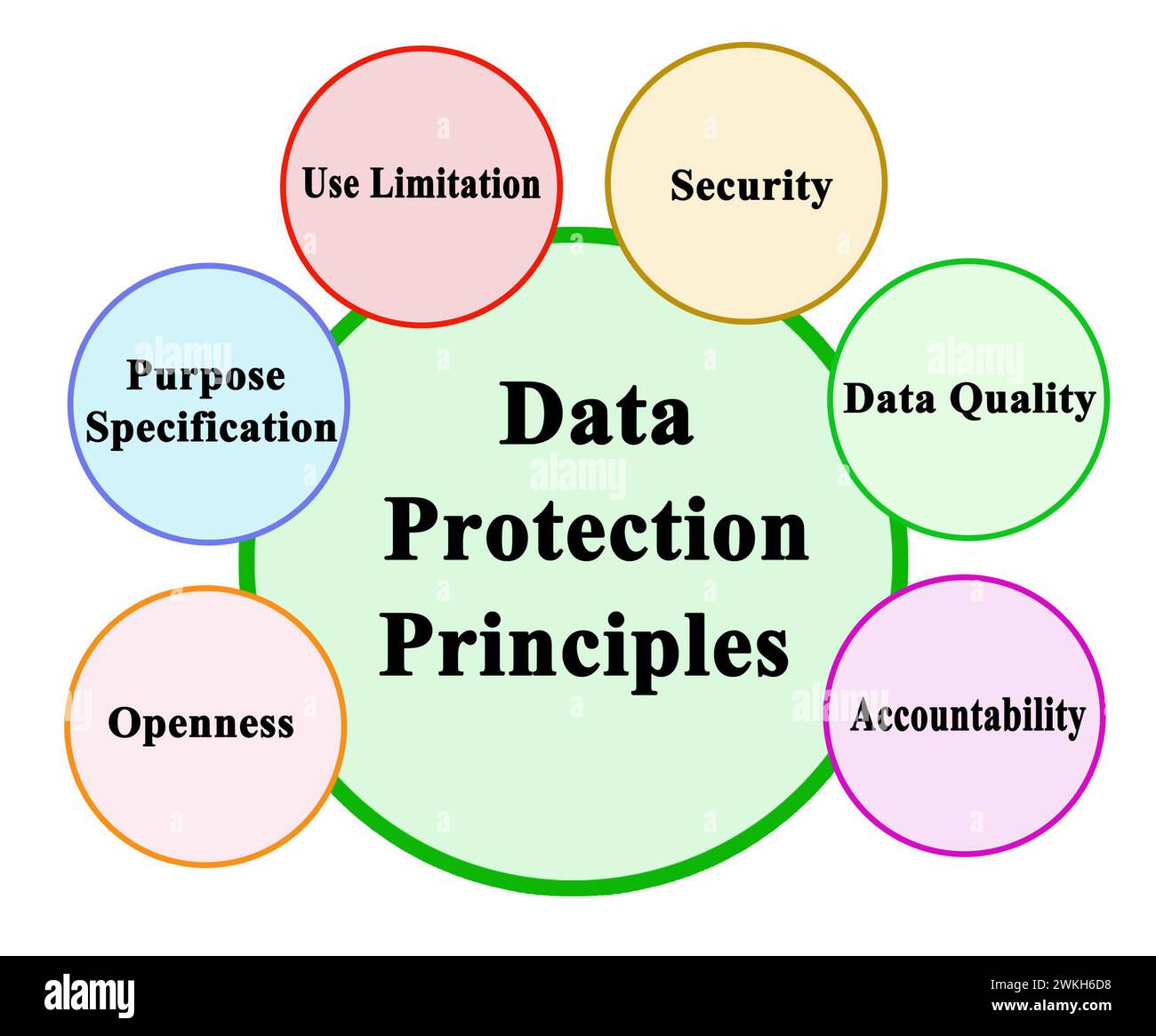
As we can see from the illustration, Best Practices For Data Protection has many fascinating aspects to explore.
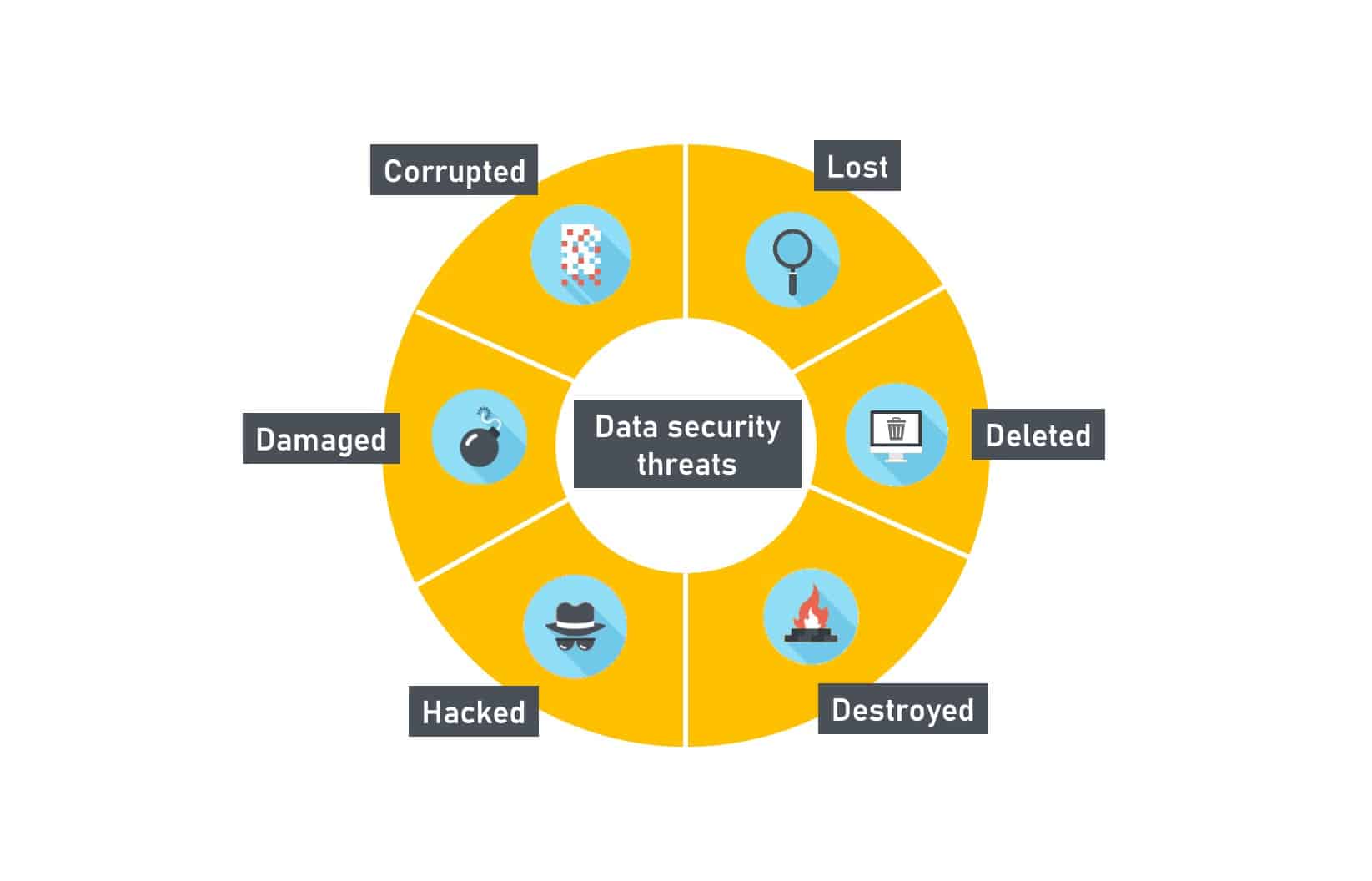
- Regular backups of data allow for quick recovery in the event of a breach or system failure, minimizing the risk of data loss. *Training and Awareness
- Educating employees on best practices for data protection helps prevent human error, a significant contributor to data breaches.Compliance and Governance
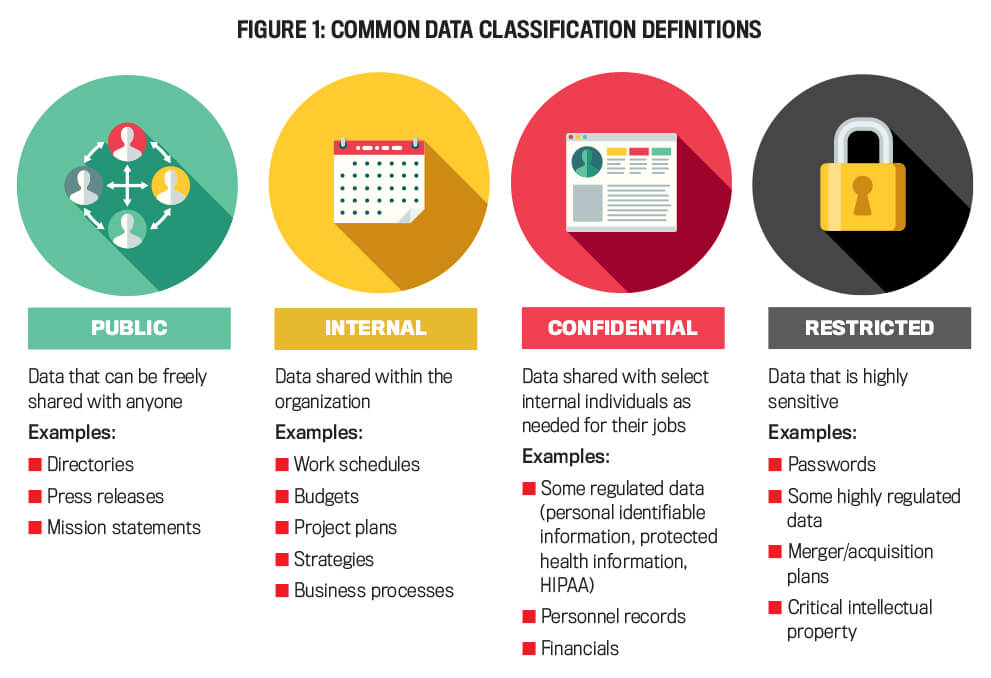
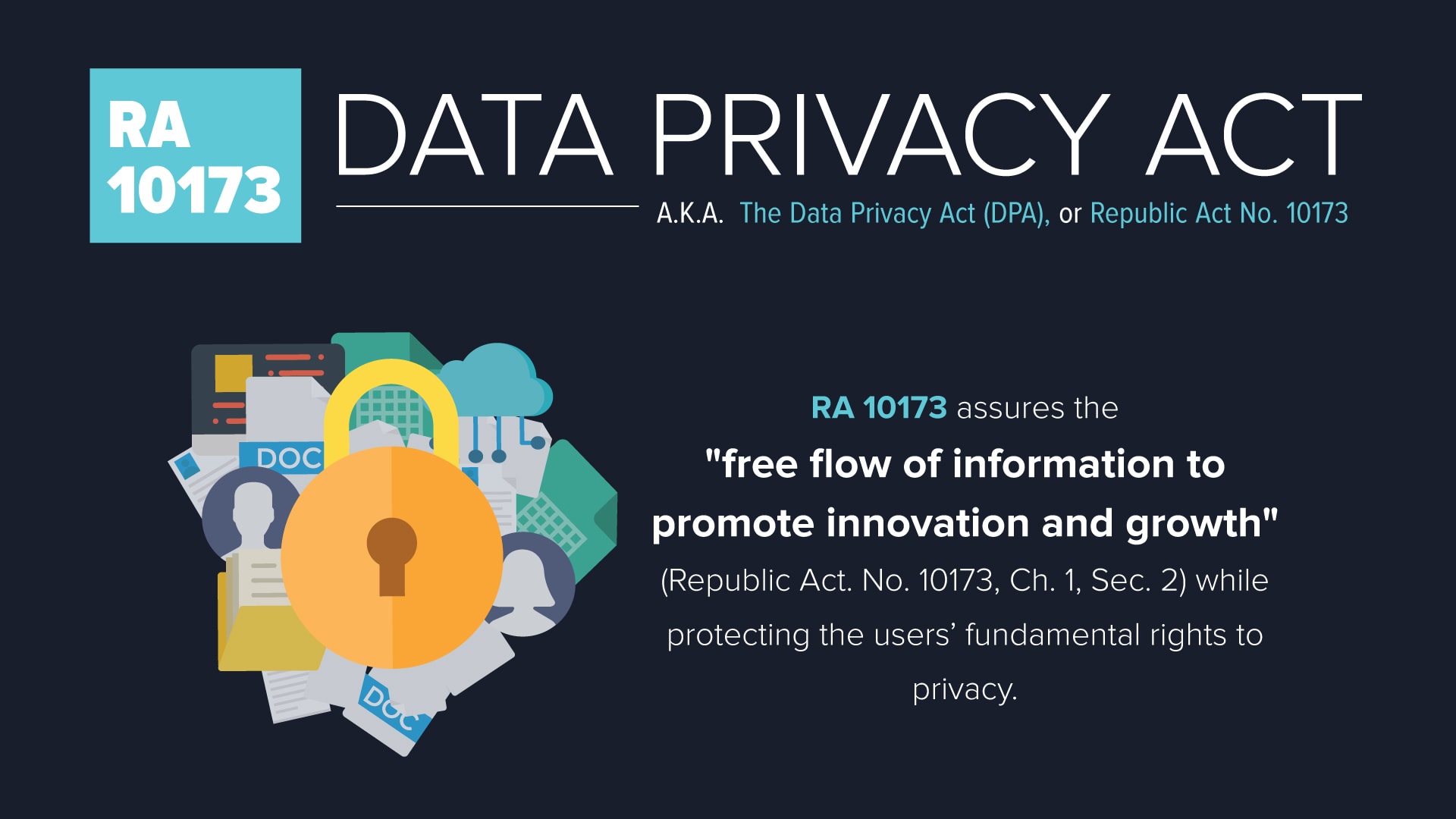
Protecting sensitive data requires structured policies and compliance strategies. Organizations must adhere to relevant regulations, such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA). Establishing a governance framework that outlines roles and responsibilities, as well as a clear data usage policy, is essential for reducing security risks.Monitoring and Incident Response
Regular monitoring and incident response planning are critical components of a robust data protection strategy. Organizations must implement processes for detecting and responding to potential security incidents, including data breaches, to minimize the impact and ensure swift recovery.Stay Ahead of Cyber Threats
Furthermore, visual representations like the one above help us fully grasp the concept of Best Practices For Data Protection.
Incorporating the latest threat intelligence and attack data into security practices is essential for staying ahead of evolving cyber threats. This includes implementing new security measures, such as controls that support cyber resiliency and secure systems design.















.jpeg)