What Is Wi-Fi Protected Setup (WPS)?
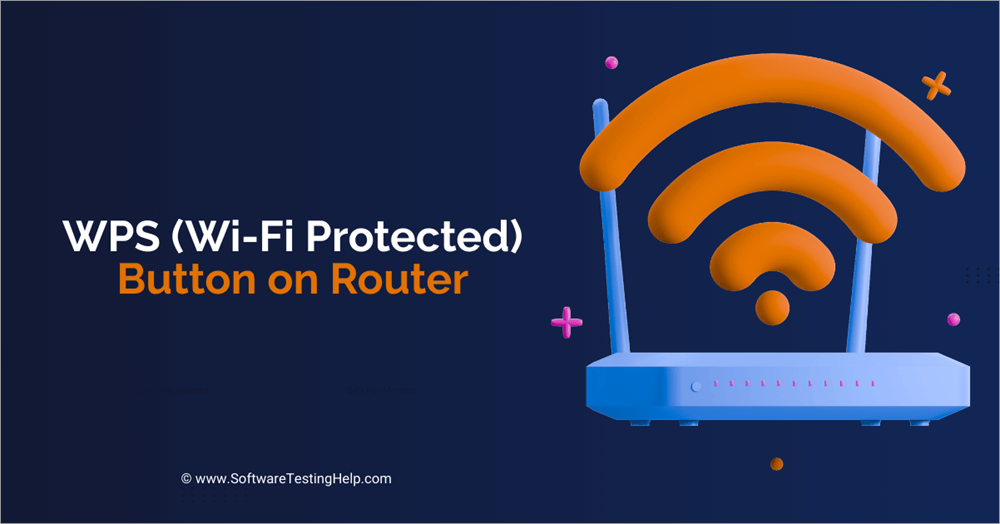
The WPS button on your router is a simple method for connecting your wireless devices when you don't want to connect manually. Learn about the standard for easing the setup of Wi-Fi networks in home and small office environments. Find out the modes, methods, and security issues of WPS, as well as the technical architecture and protocol of the standard.How Does Wi-Fi Protected Setup Work?
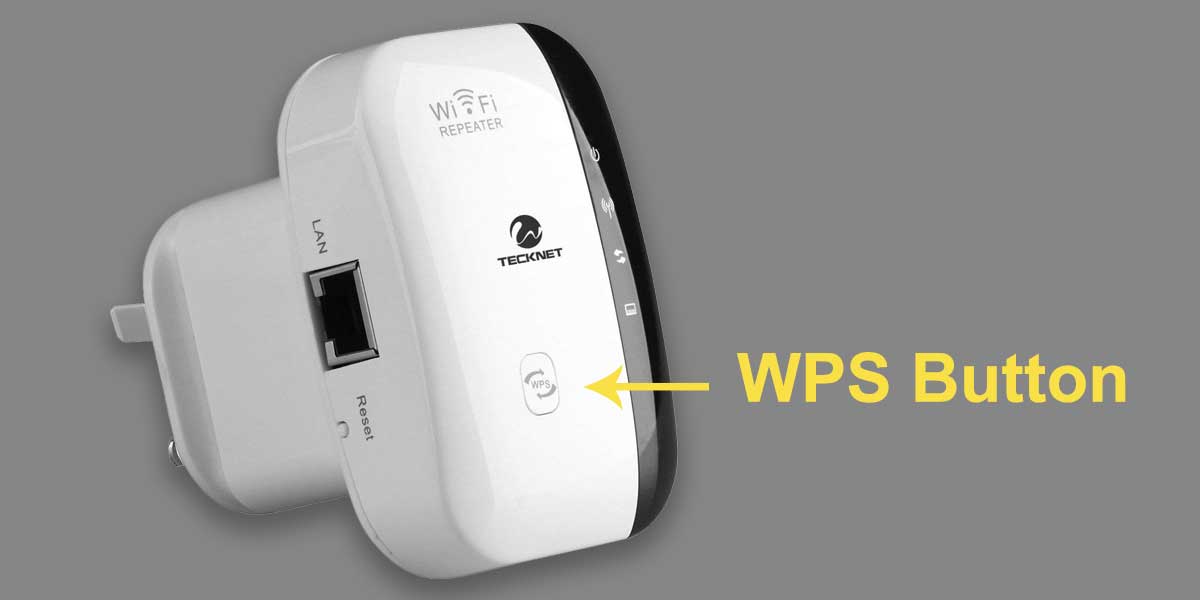
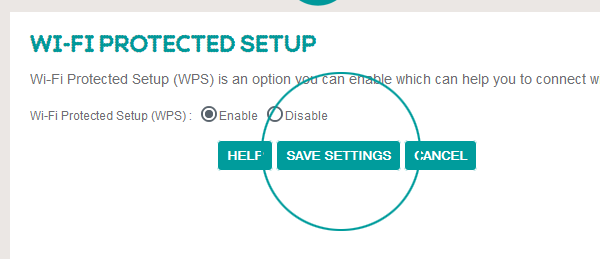
Wi-Fi Protected Setup (WPS) is a feature that allows devices to join a router without sharing the password. It's a network security standard that simplifies the process of connecting devices to a wireless network. The WPS button is often found on the back or side of routers. When you press it, the router enters a short 1-2 minute window where nearby devices can automatically connect.Security Issues with WPS
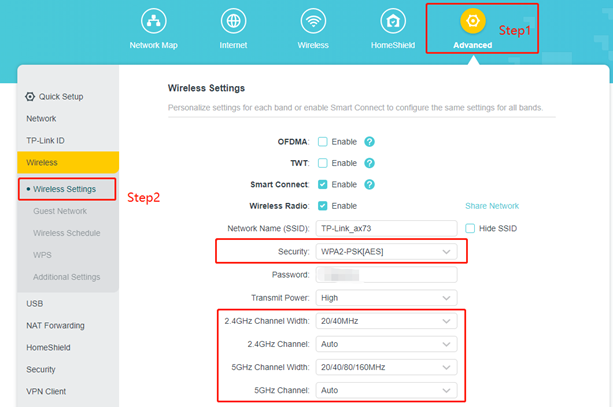
While WPS is designed to simplify the process of setting up home network security, flaws in how it was implemented limit its usefulness. With WPA2 and WPS disabled, an attacker needs to determine the WPA2 PSK that the clients use, which is a time-consuming process. However, if WPS is enabled, an attacker can use various techniques to brute-force the WPS PIN, potentially gaining unauthorized access to the network. To securely use WPS on your router, follow these steps: 1. Ensure that your router has WPA2 and WPS disabled. 2. Change the default admin password on your router. 3. Set up Wi-Fi Protected Setup (WPS) with a strong connection method, such as a PIN or a TOUCH screen. 4. Use a network scanning tool to detect and block any unauthorized devices. 5. Regularly update your router's firmware and network settings.Technical Architecture and Protocol
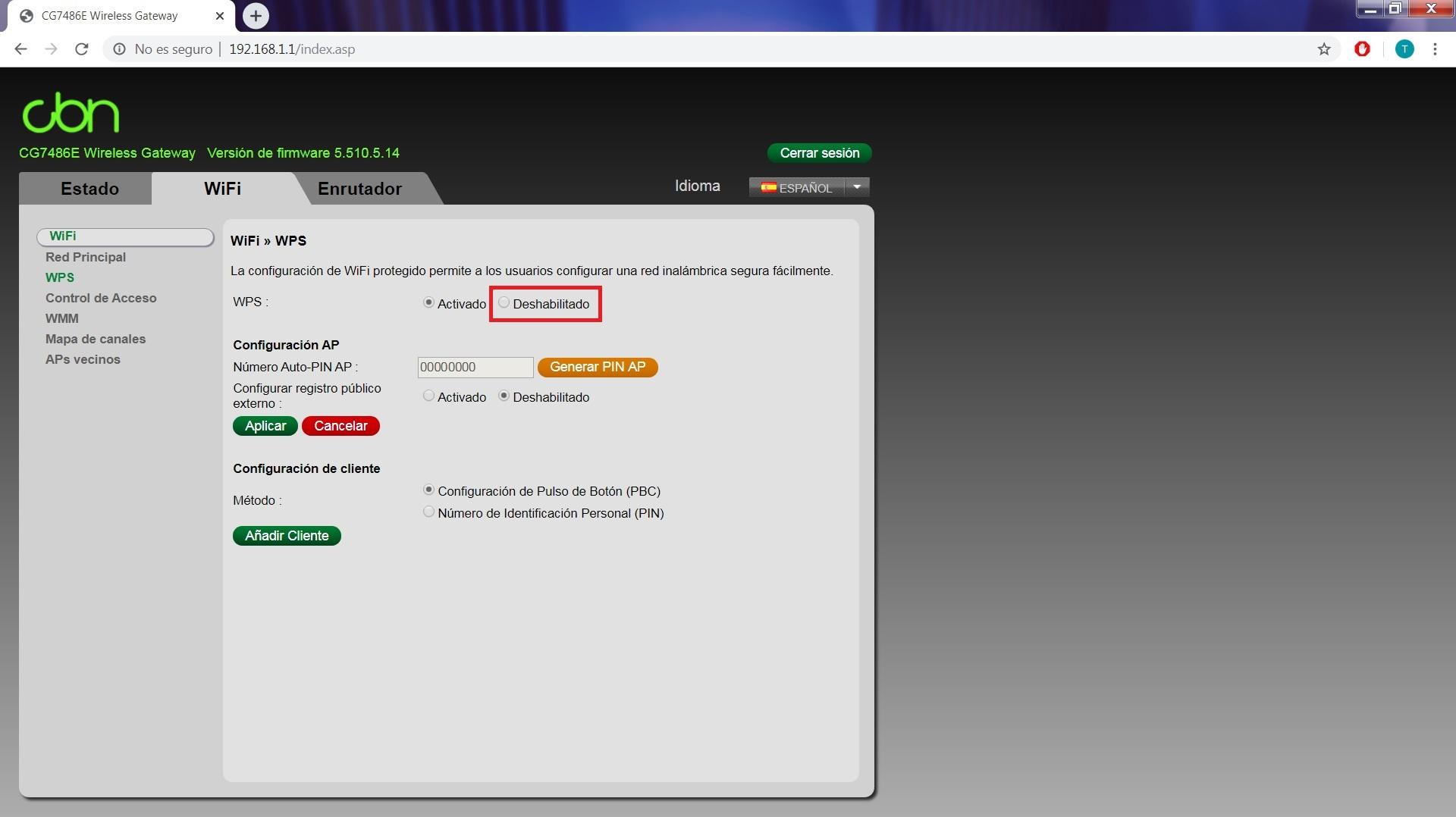
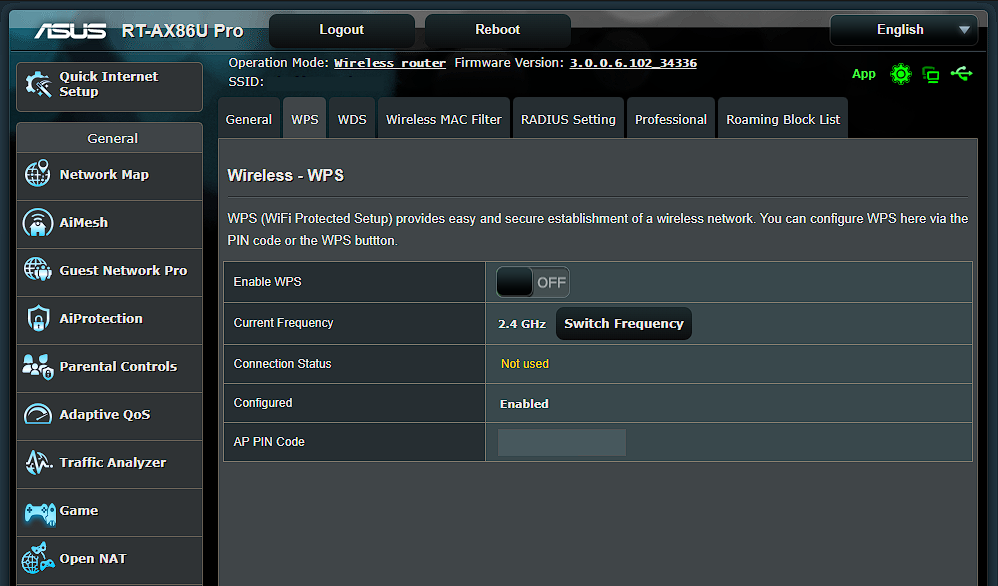
Furthermore, visual representations like the one above help us fully grasp the concept of Wi-Fi Protected Setup.
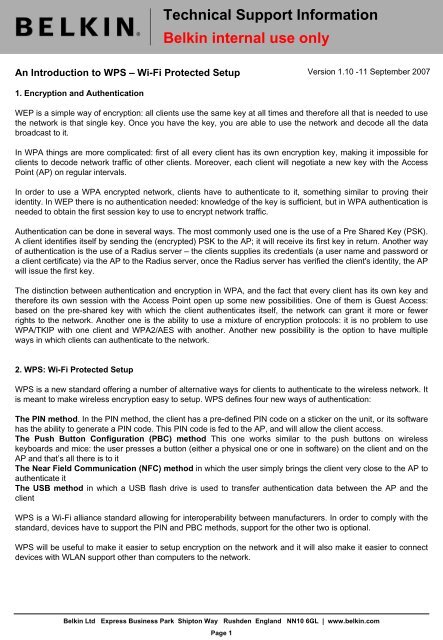
The encryption method in WPS is WEP and WPA. Wireless networks employing WPS require access points and devices to generate a unique Pre Shared Key (PSK) configured during setup. However, WPS security loophole lets hackers bypass Wi-Fi passwords in just 2 minutes or less. Connecting via WPS invocation prevents exploiting denial of service threats originating while using it network features.WPS Methods
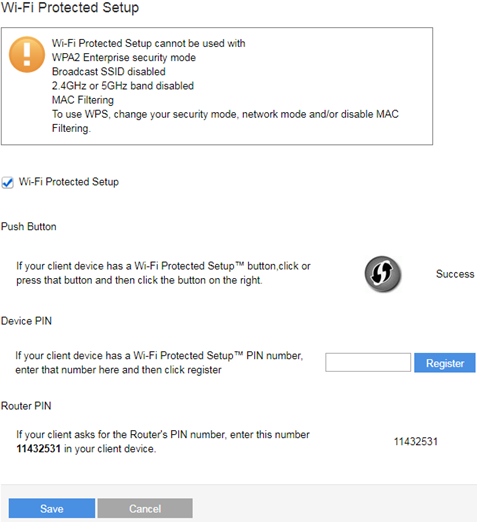
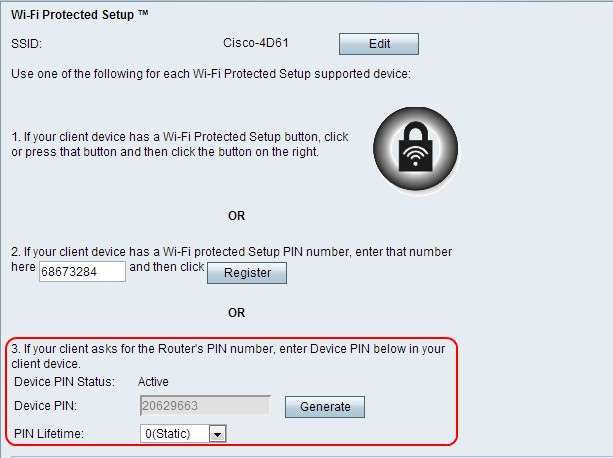
There are two methods of configuring WPS: 1. **Push Button Method (PBC):** One device clicks a button, and the other clicks its button within 2 minutes. Once this occurs, a unique PIN code is generated allowing the second device to pair with the Wi-Fi network. 2. **Personal Identification Number (PIN) Method:** Each device has a unique PIN, and they must match. To ensure seamless connections, users can enter PIN codes manually or use a standard configuration WPS service, enabling fast implementation directly on the device. WPS is the standard for quickly and securely adding new devices. Depending on HP printer instructions.Push Button Configuration (PBC)
All devices on the network have a numeric code known as a PIN in order to initiate WPS. The push button configuration mode will yield in less time of a maintenance process when the devices may create multiple WPS uses.WPS and HP Printers
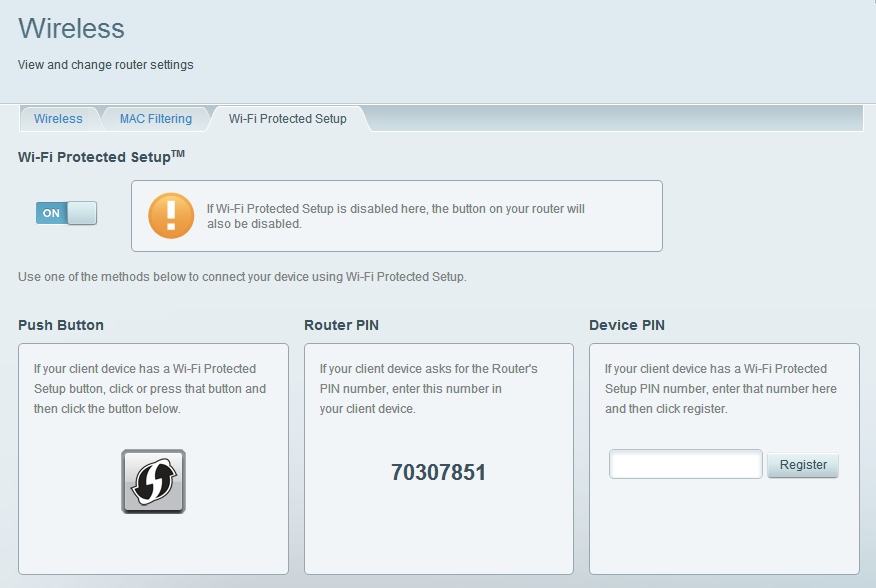
Moving forward, it's essential to keep these visual contexts in mind when discussing Wi-Fi Protected Setup.
HP printers support Wi-Fi Protected Setup (WPS) for easy wireless connectivity. The following steps are for an HP DeskJet printer. *- Press and hold the Wireless button
- While still holding the Wireless button, press the cancel button to display menu options
- Release the Wireless button
- Select "Wi-Fi Setup Wizard"
- Repeat the process on the connected HP printer.