How to Prevent Identity Theft from Shadow Fails
Identity theft has become a rapidly growing threat in the digital age, with numerous methods for thieves to obtain sensitive information. One particular tactic, known as "shadow fails," involves exploiting vulnerabilities in organizations' security systems, posing a significant risk to individual identities. In this article, we will explore what shadow fails are, how they occur, and most importantly, provide actionable tips on how to prevent identity theft from these malicious attacks.
What are Shadow Fails?
Shadow fails refer to the unauthorized access to sensitive information and systems, often resulting from compromised security measures or unmonitored user accounts. This can occur due to a variety of factors, such as weak passwords, unpatched software vulnerabilities, or poorly configured network permissions. When an individual's identity is compromised through a shadow fail, they may inadvertently grant access to unauthorized individuals or groups, who can then exploit this vulnerability to steal sensitive information.
Such details provide a deeper understanding and appreciation for How To Prevent Identity Theft From Shadow Fails.
How Do Shadow Fails Happen?
Shadow fails often occur due to the following reasons:
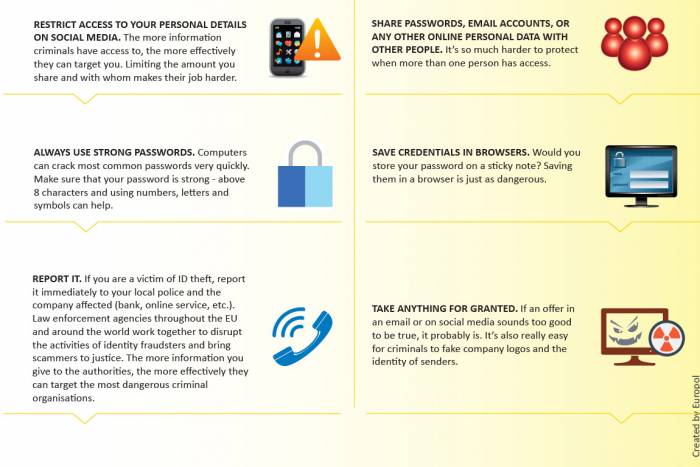
- Insufficient security protocols: Failing to implement robust security measures, such as firewalls, intrusion detection systems, or multi-factor authentication.
- Lack of user awareness: Employees or users may inadvertently click on phishing emails, open malicious attachments, or enter credentials into fake login pages.
- Weak passwords and account management: Using easily guessable passwords or failing to update them regularly, leading to compromised account access.
- Unpatched software vulnerabilities: Failing to patch software vulnerabilities, making it easier for attackers to exploit these weaknesses.

Moving forward, it's essential to keep these visual contexts in mind when discussing How To Prevent Identity Theft From Shadow Fails.
How to Prevent Identity Theft from Shadow Fails
Organizational Measures:
- Implement robust security protocols, including firewalls, intrusion detection systems, and multi-factor authentication.
- Regularly update software and patches to ensure vulnerabilities are addressed.
- Conduct regular user training sessions to educate employees on security best practices and the importance of maintaining secure passwords.
- Establish a comprehensive identity and access management (IAM) system to monitor and control user access to sensitive resources.

Individual Measures:
- Use strong passwords and maintain regular password updates.
- Be cautious when clicking on links or opening attachments from unknown sources.
- Regularly monitor personal financial accounts and credit reports for suspicious activity.
- Use reputable antivirus software and keep it updated to protect against malware and other online threats.
- Stay informed about the latest security best practices and scams.
Shadow fails pose a significant threat to individual identities, and it is crucial to take proactive measures to prevent these malicious attacks. By implementing robust security protocols, educating employees, and maintaining individual vigilance, we can significantly reduce the risk of identity theft from shadow fails. Remember, your identity is only as secure as the measures you take to safeguard it.