Cybersecurity for Online Charity Donations: Safeguarding Donor Data and Building Trust
Why Cybersecurity Matters for Nonprofits
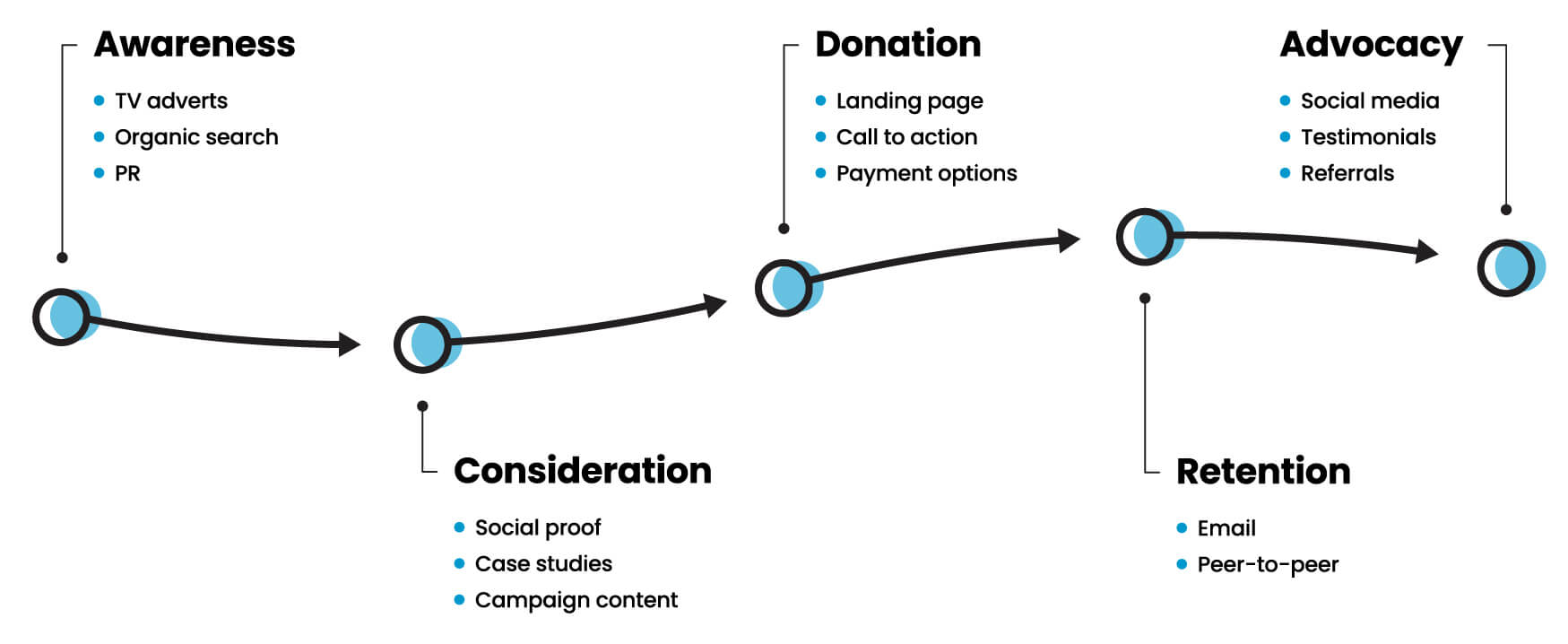
Nonprofit organizations often handle sensitive information, including donor data, financial records, and personal details of beneficiaries. This makes them attractive targets for cybercriminals who seek to exploit vulnerabilities for financial gain or to disrupt operations. A successful cyberattack can compromise donor data, damage a nonprofit's reputation, and even put its mission continuity at risk.
Common Cyber Threats Facing Nonprofits

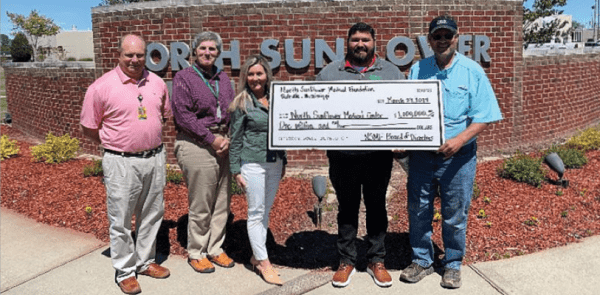
This particular example perfectly highlights why Cybersecurity For Online Charity Donations is so captivating.
- Phishing attacks: Scammers use fake emails, texts, or social media messages to trick donors into revealing sensitive information.
- Malware attacks: Malware can infiltrate a nonprofit's system, stealing data or disrupting operations.
- Data breaches: Unauthorized access to donor data can lead to identity theft, fraud, and reputational damage.
- Carding attacks: Hackers target online donations, attempting to steal payment card information.
- Scams: Sophisticated scammers use fake charities, mimic real ones, or pose as donors to trick nonprofits into sending funds.
Essential Cybersecurity Practices for Nonprofits
To safeguard donor data and ensure compliance, nonprofits must implement robust cybersecurity measures. Here are five practical, foundational steps:

As we can see from the illustration, Cybersecurity For Online Charity Donations has many fascinating aspects to explore.
- Implement robust data encryption**: Protect sensitive information with end-to-end encryption, both in transit and at rest.
- Use secure online donation platforms**: Choose platforms with robust security features, such as encryption, two-factor authentication, and compliance with industry standards (e.g., PCI-DSS).
- Conduct regular security audits and penetration testing**: Identify vulnerabilities and ensure that systems, networks, and applications are patched and updated.
- Educate staff and donors on cybersecurity best practices**: Raise awareness about phishing, malware, and other threats to prevent human error and ensure compliance with security protocols.
- Develop incident response and disaster recovery plans**: Be prepared to respond to cyber incidents and data breaches, minimizing downtime and reputational damage.
Benefits of Prioritizing Cybersecurity
By prioritizing cybersecurity, nonprofits can:
- Protect donor data and prevent identity theft
- Maintain the trust of supporters and donors
- Ensure compliance with regulations and industry standards
- Prevent reputational damage and loss of revenue
- Enhance overall security and resilience
Conclusion
Cybersecurity is no longer a luxury, but a necessity for nonprofit organizations. By prioritizing cybersecurity measures, nonprofits can safeguard donor data, ensure compliance, and build trust with their supporters. By understanding the common cyber threats, implementing essential cybersecurity practices, and prioritizing education and incident response, nonprofits can maintain the integrity of their mission and protect the well-being of their supporters.