Configuring a G Network for Secure Access to Data
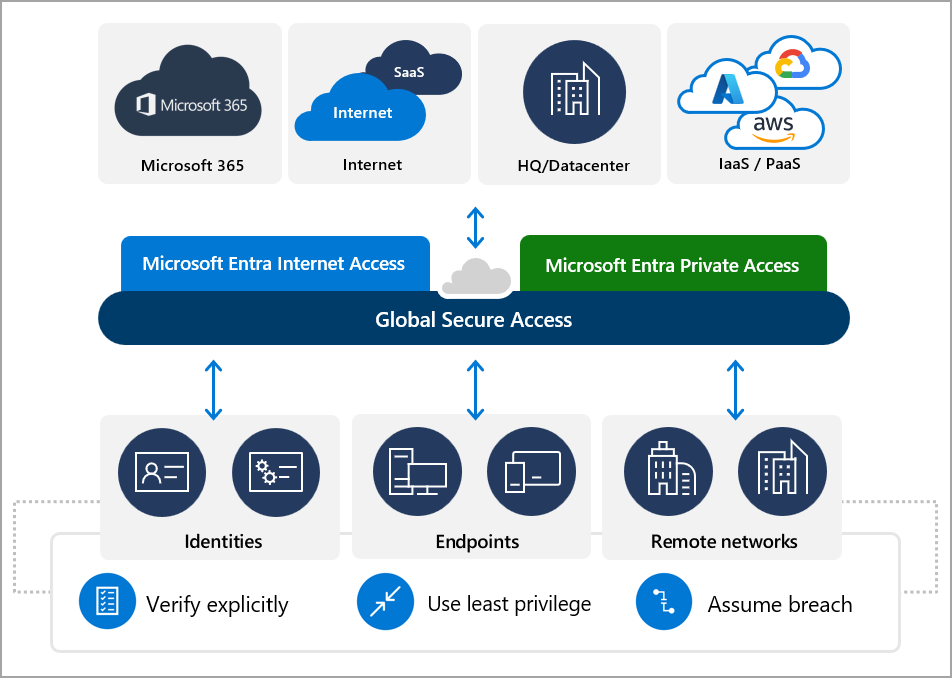
In today's digital landscape, ensuring the security and integrity of sensitive data is paramount. With the rise of remote work and the increasing reliance on cloud-based services, organizations must implement robust security measures to protect their data from unauthorized access. One such measure is configuring a G Network for secure access to data, which provides a secure and scalable solution for organizations to protect their data and systems.What is a G Network?
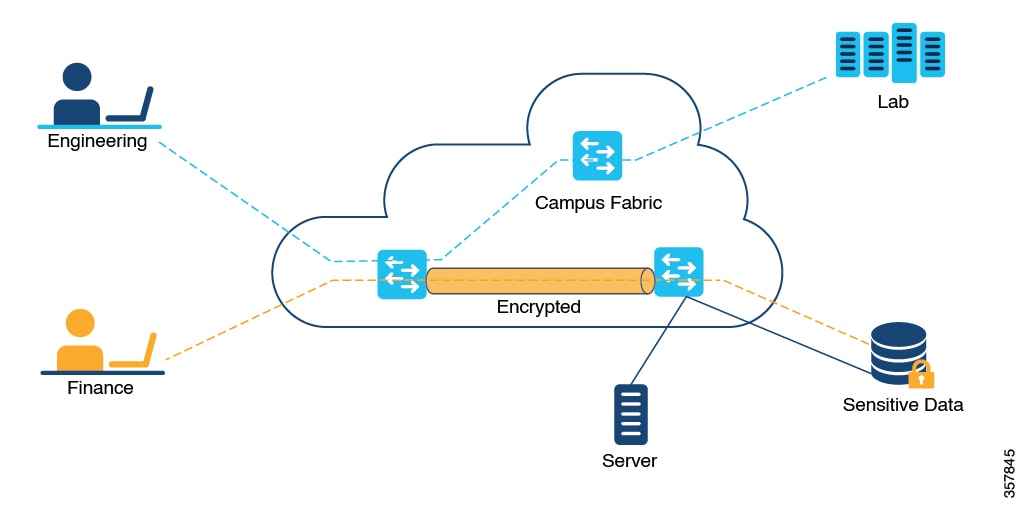
A G Network, short for Global Secure Access, is a cloud-based network security platform that provides secure access to data, applications, and systems for remote users and branch offices. It is designed to provide fast and secure access to business-critical applications and data, while preventing unauthorized access and ensuring compliance with regulatory requirements.Benefits of Configuring a G Network
Configuring a G Network offers numerous benefits for organizations, including: * *Increased productivity: With a G Network, remote users and branch offices can access business-critical applications and data securely and reliably, improving productivity and efficiency.
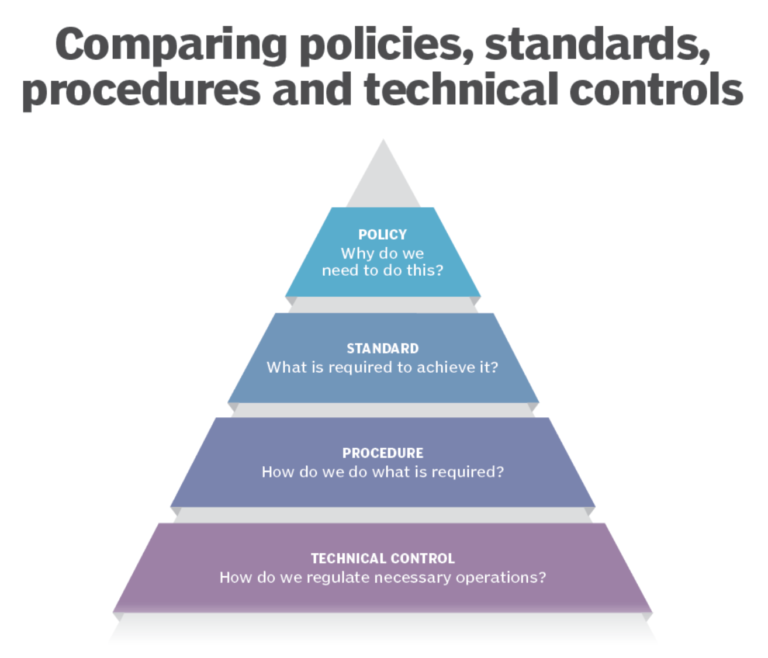
*Enhanced compliance: A G Network helps organizations meet regulatory requirements by providing secure access to data and systems, reducing the risk of non-compliance.
*Scalability: A G Network can scale to meet the growing needs of an organization, providing a secure and flexible solution for access to data and applications.
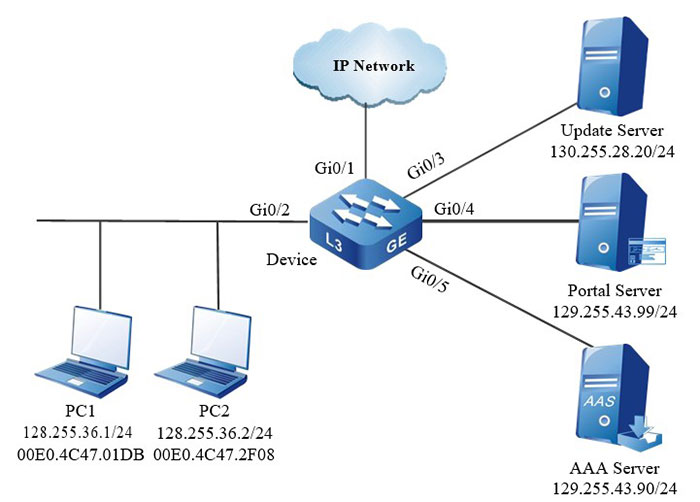
As we can see from the illustration, Configuring A G Network For Secure Access To Data has many fascinating aspects to explore.
Step-by-Step Guide to Configuring a G Network
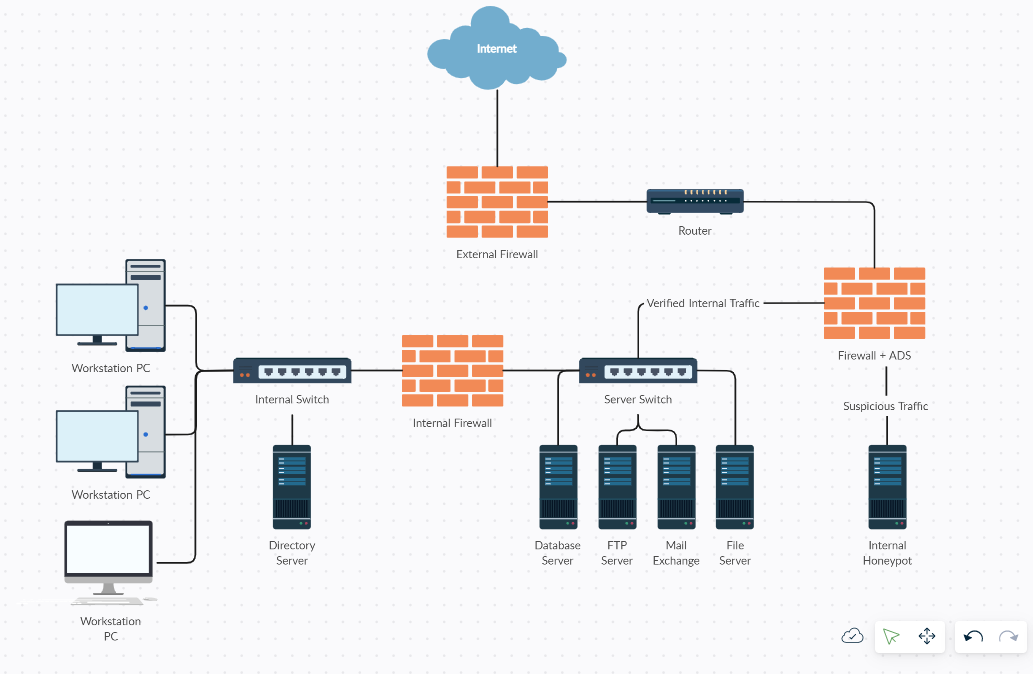
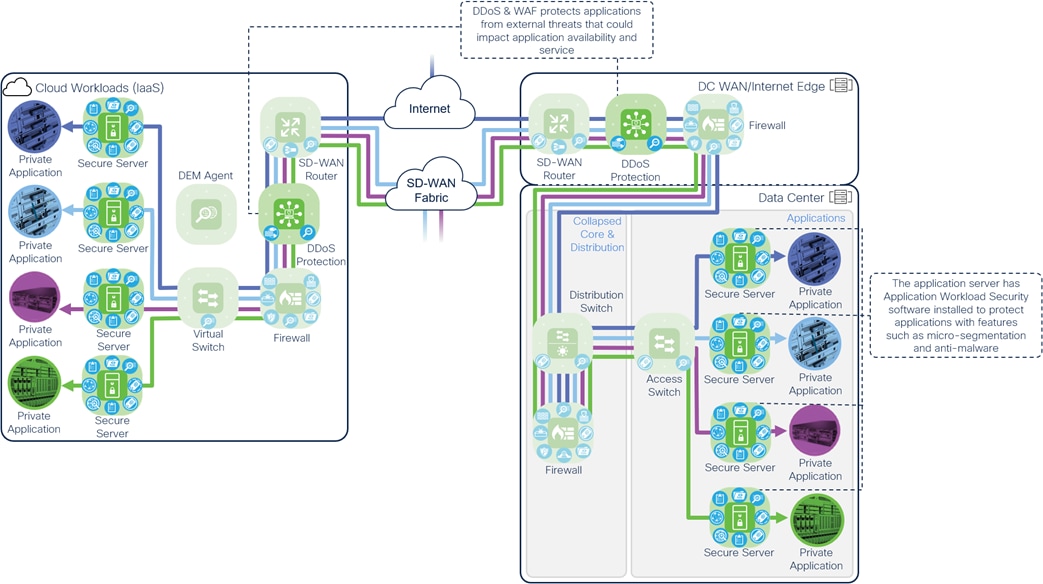
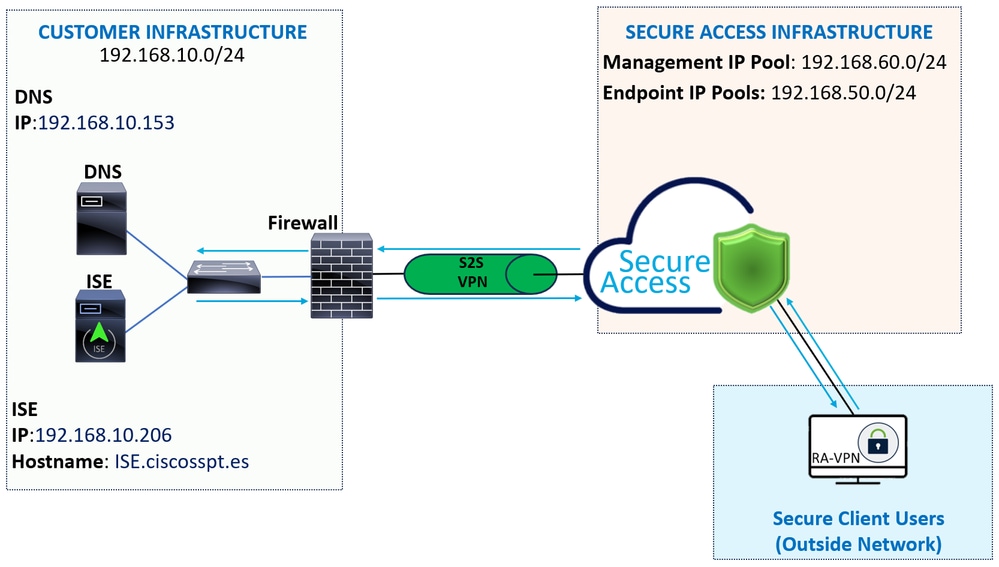
Configuring a G Network involves several steps, including: *Step 1: Plan and Design
+Determine the scope and requirements of the project.
+Assess the current network infrastructure and identify potential security risks.
+Design a secure and scalable network architecture that meets the organization's needs.
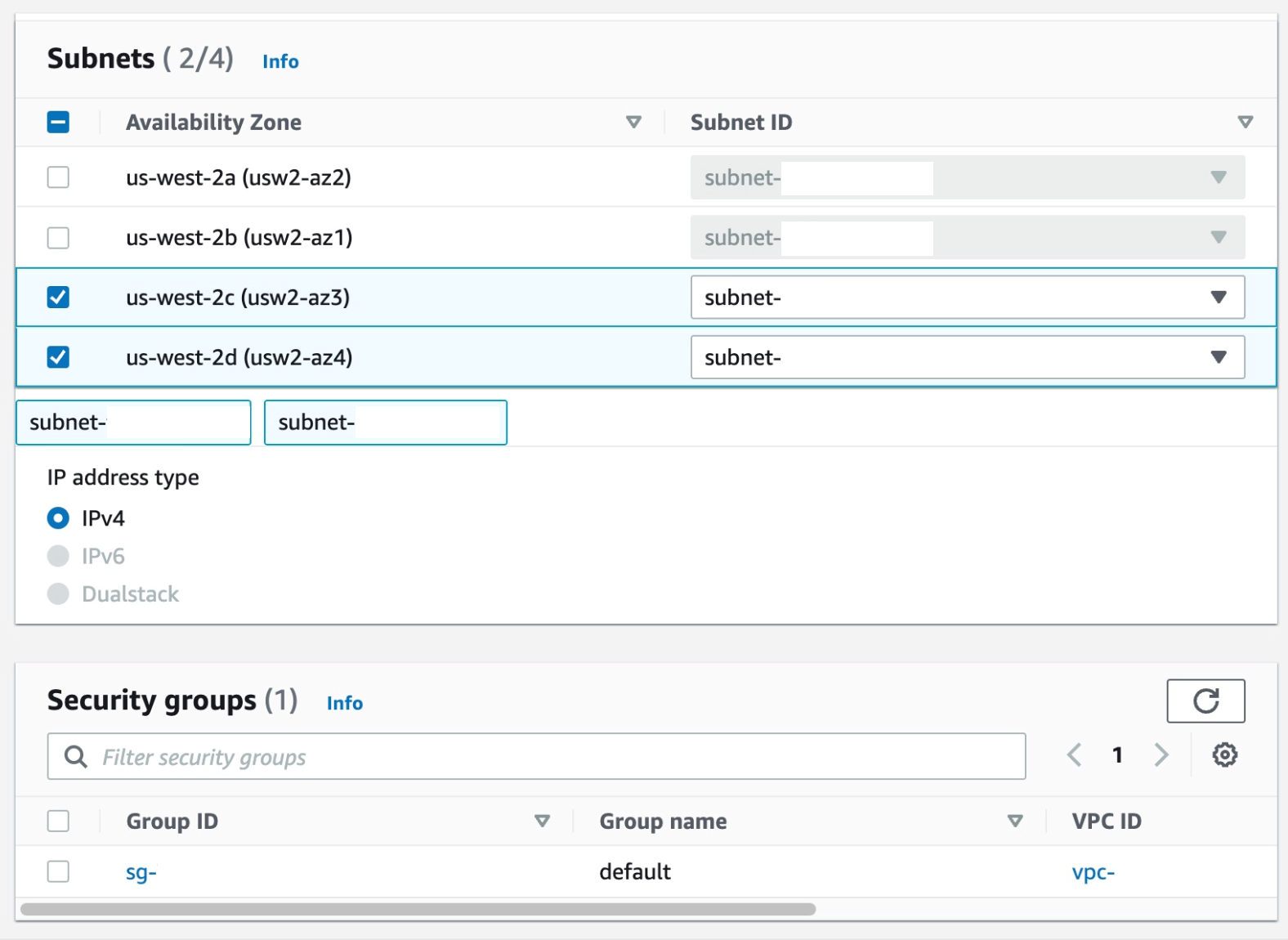
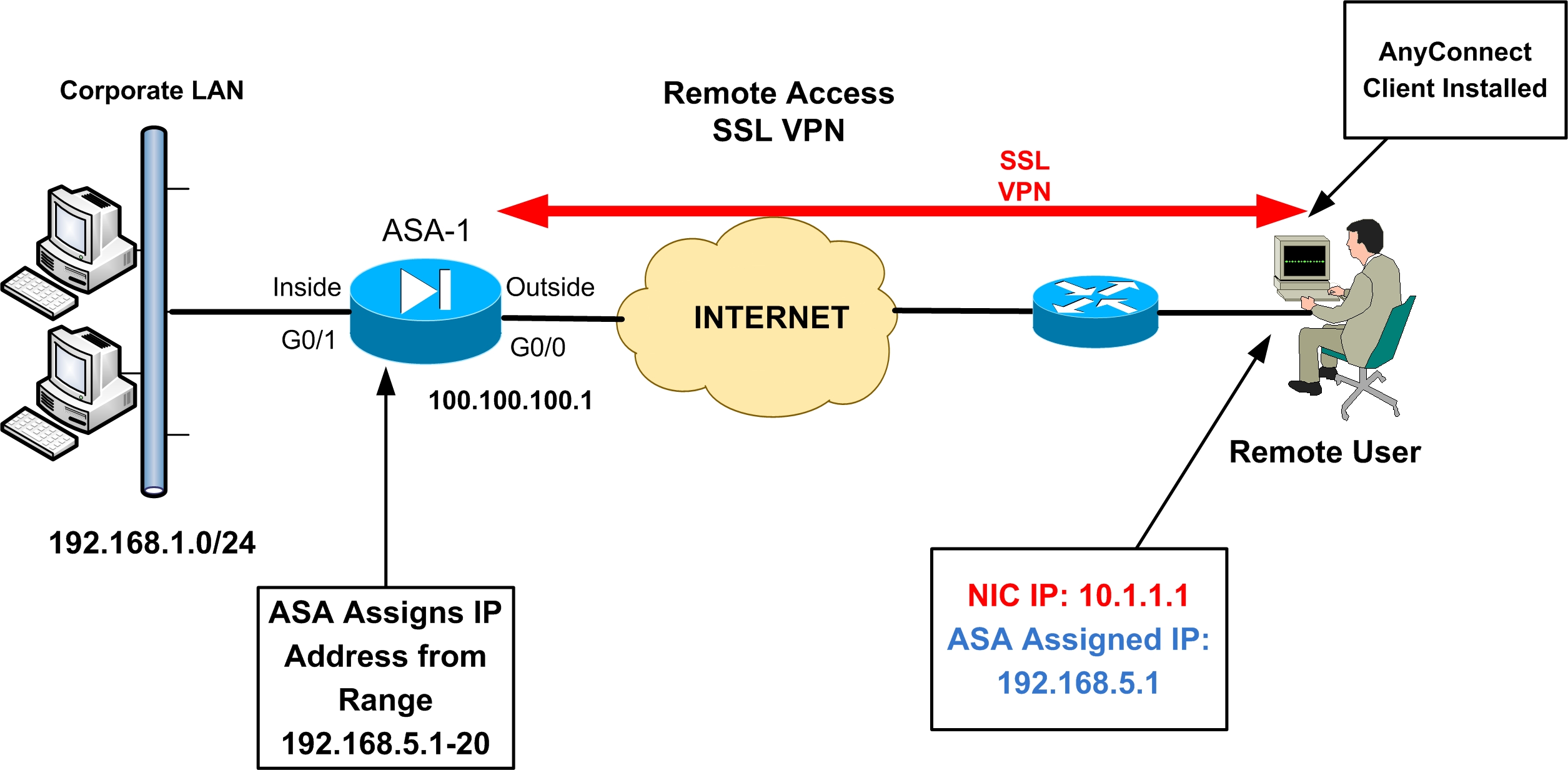
Step 2: Deploy the G Network
+Deploy the G Network infrastructure, including the necessary hardware and software components.
+Configure the G Network to connect to the organization's existing network infrastructure.
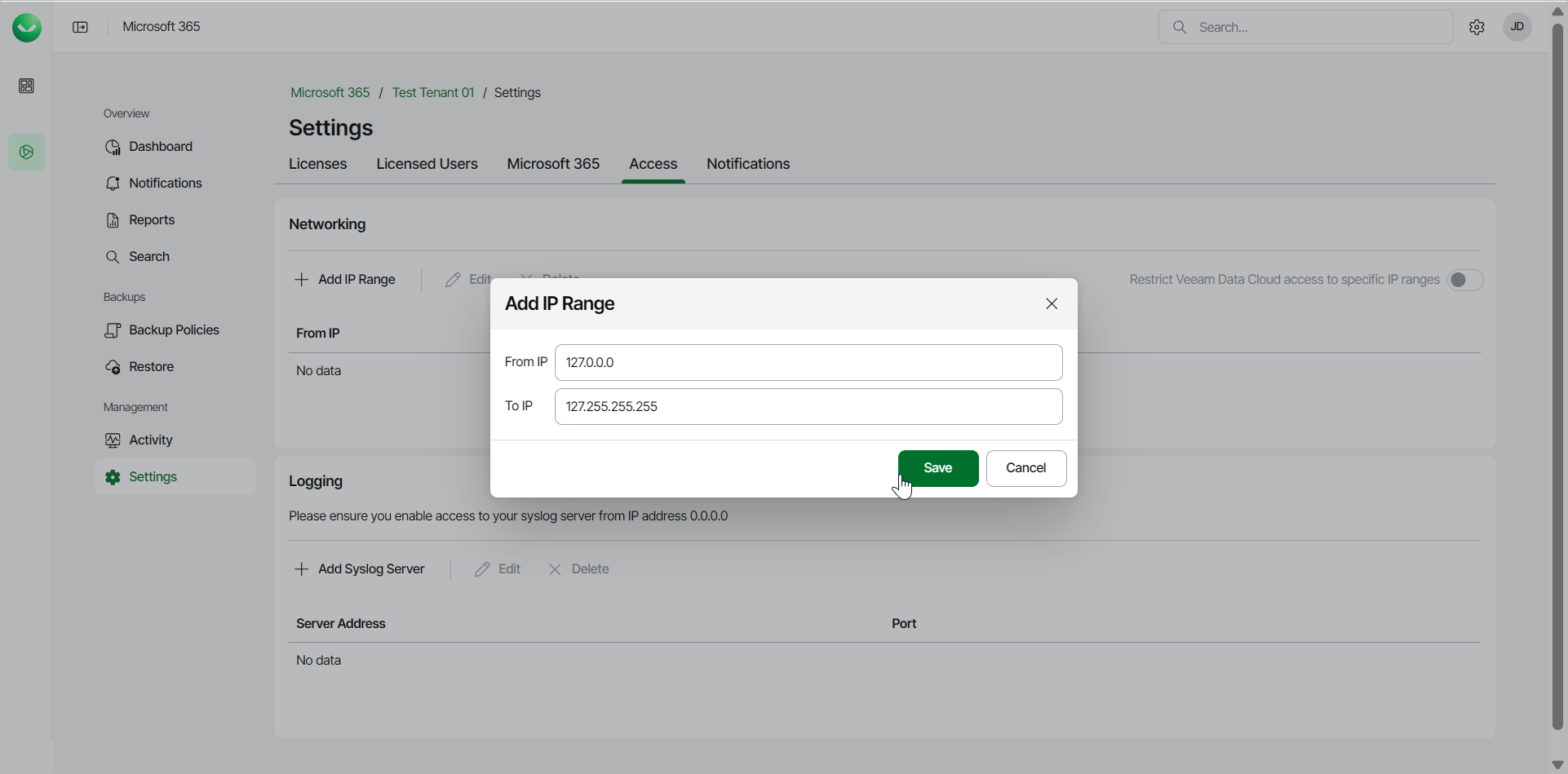
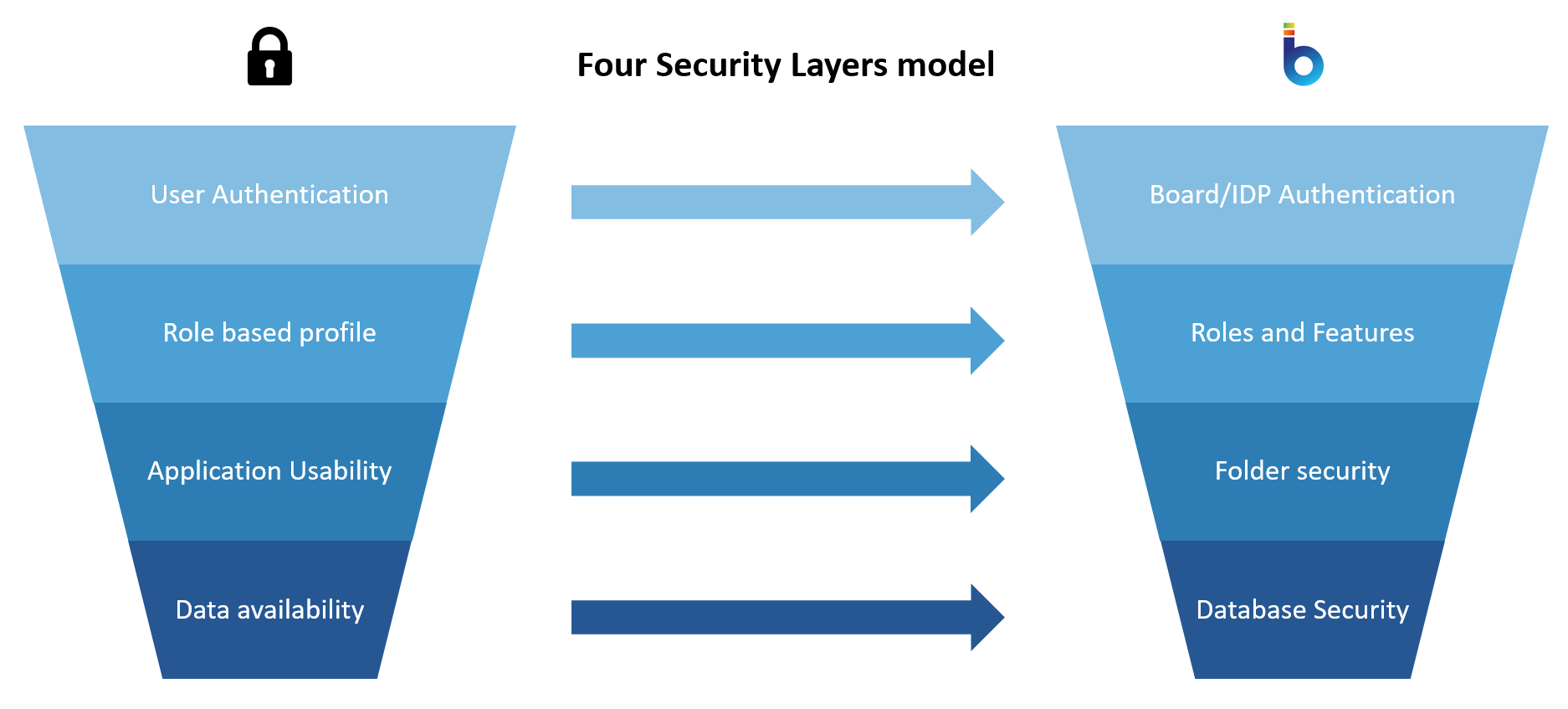
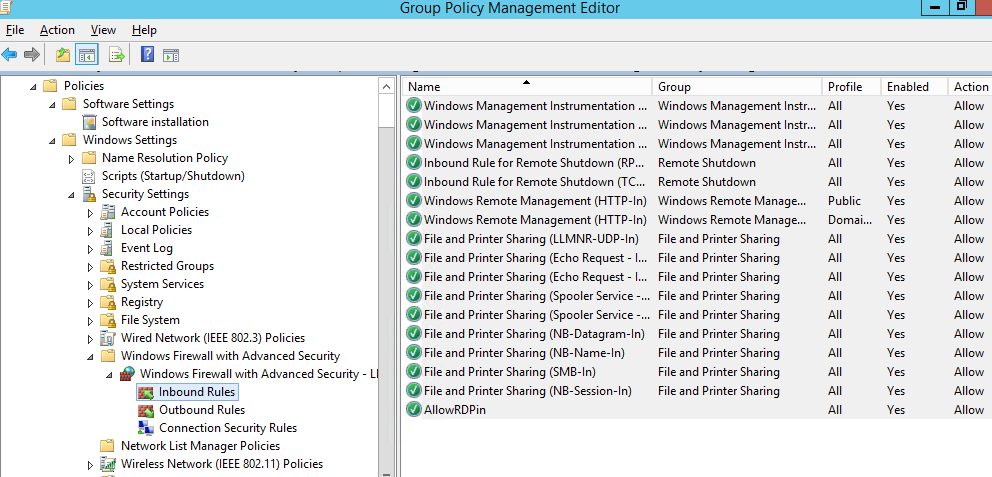
*Step 3: Configure Access Controls
+Configure user access controls, including authentication and authorization policies.

Implement access controls for data and applications, including encryption and access limits.
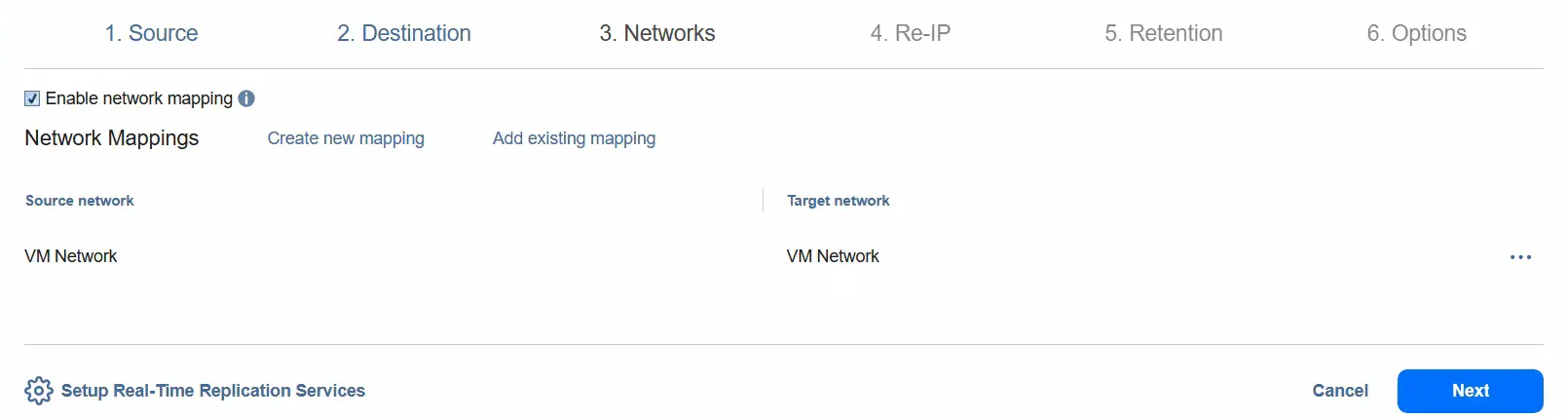
*Step 4: Monitor and Maintain
+Monitor the G Network for security threats and anomalies.
+Perform regular maintenance tasks to ensure the G Network remains secure and up-to-date.
* +Test the G Network to ensure it meets the organization's requirements.
+Validate the G Network's security and performance.