Keeping My Phone Secure from Hackers: Essential Tips and Strategies
The Growing Threat of Phone Hacking
In today's digital age, our smartphones are an essential part of our daily lives. We use them for communication, entertainment, and to access sensitive information. However, with the increasing reliance on mobile devices comes a growing threat of phone hacking. Hackers are becoming more sophisticated, and their tactics are evolving to target smartphones. To keep your phone secure from hackers, it's essential to develop a strategy for protecting your personal information.Understand the Risks

Basic Phone Security Measures
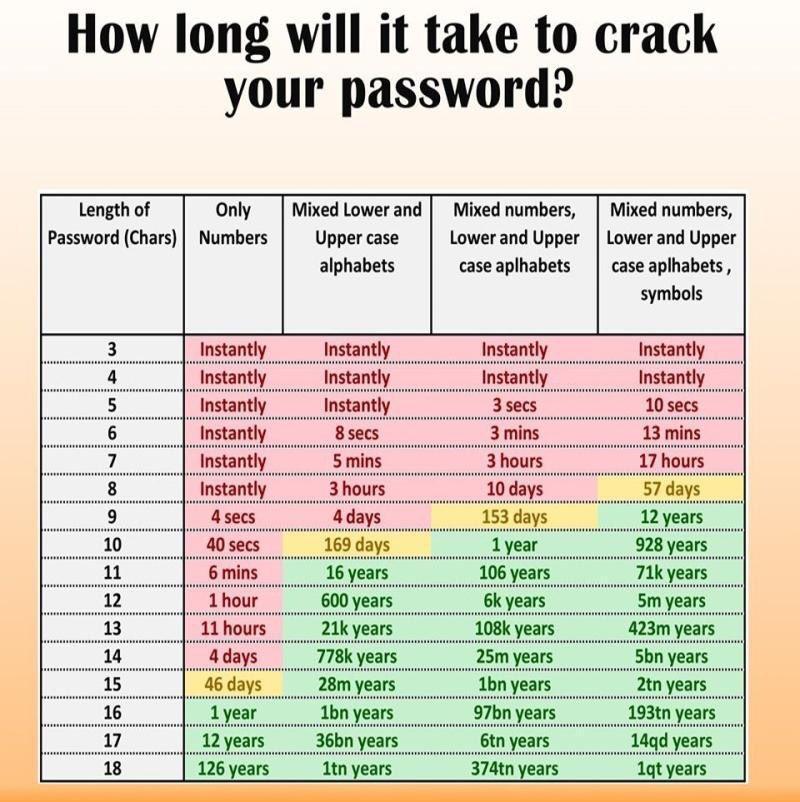
Here are some basic phone security measures that you should implement:- Password protection: Set a strong and unique password for your phone, and enable biometric authentication (e.g., fingerprint or facial recognition) for added security.
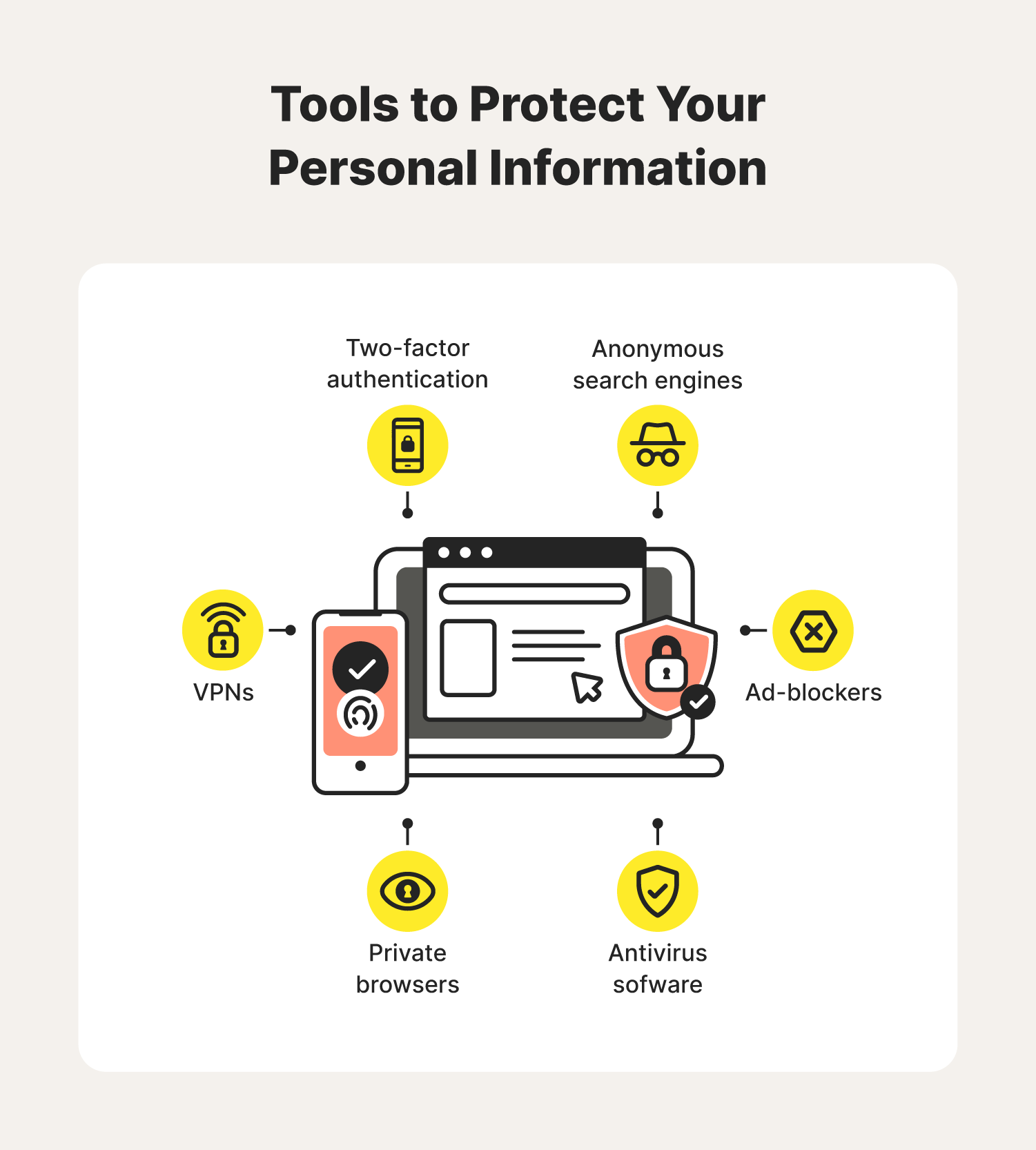
- Two-factor authentication (2FA): Enable 2FA for your phone and other online accounts to add an extra layer of security.
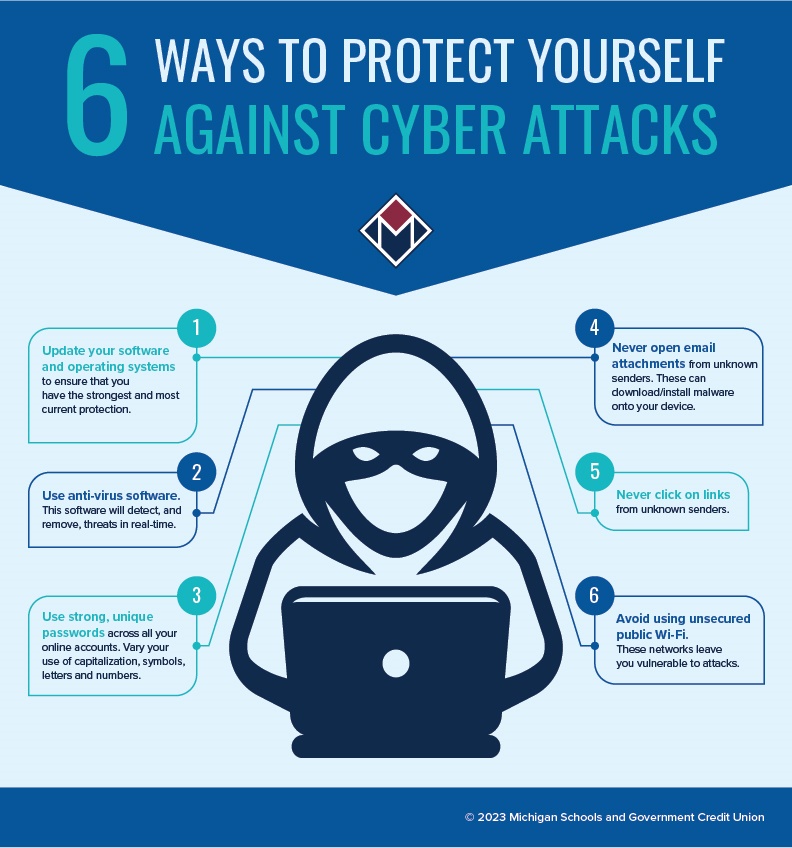
- Regular software updates: Keep your phone's operating system and apps up to date, as updates often include security patches and bug fixes.
- Antivirus software: Install and regularly update antivirus software to protect your phone from malware and other threats.
- App permissions: Be cautious when granting app permissions, and review the permissions granted to each app to ensure they are necessary.
- Cloud backups: Regularly back up your phone data to the cloud or a secure storage device to prevent data loss in case your phone is hacked or lost.

Advanced Phone Security Measures
To further enhance your phone's security, consider the following advanced measures:Staying Vigilant

- Be cautious with links and attachments: Avoid clicking on suspicious links or opening attachments from unknown senders, as they may contain malware or phishing scams.
- Verify app authenticity: Only download apps from trusted sources, such as the App Store or Google Play, and be wary of fake or cloned apps.
- Regularly review account activity: Regularly review your phone's account activity, including recent logins, to detect potential security breaches.
- Report suspicious activity: If you suspect your phone has been hacked or compromised, report it to your carrier, financial institutions, and other relevant parties.